F5 releases security advisory for multiple vulnerabilities including K000132893: GRUB2 vulnerability CVE-2022-28733. This flaw allows an attacker to craft a malicious packet, triggering an integer underflow in grub code.
Consequently, the memory allocation for handling the packet data may be smaller than the size needed. This issue causes an out-of-bands write during packet handling, compromising data integrity, confidentiality issues, a denial of service, and remote code execution.
Security Advisory Status
F5 Product Development has assigned ID 1209209 (BIG-IP), ID 1209209-7 (BIG-IQ), and ID 1207749-1 (F5OS) to this vulnerability.
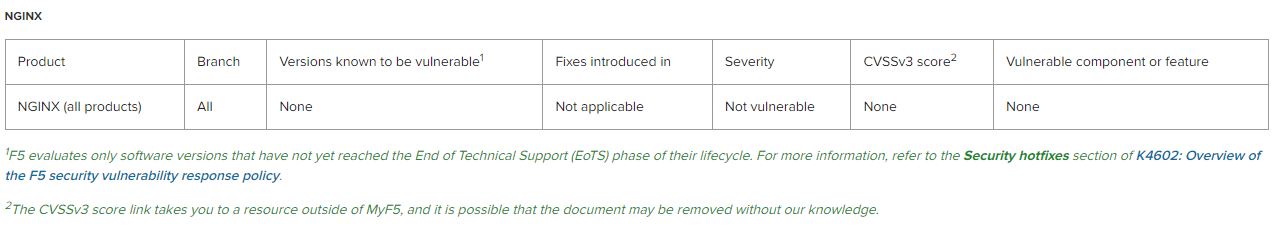
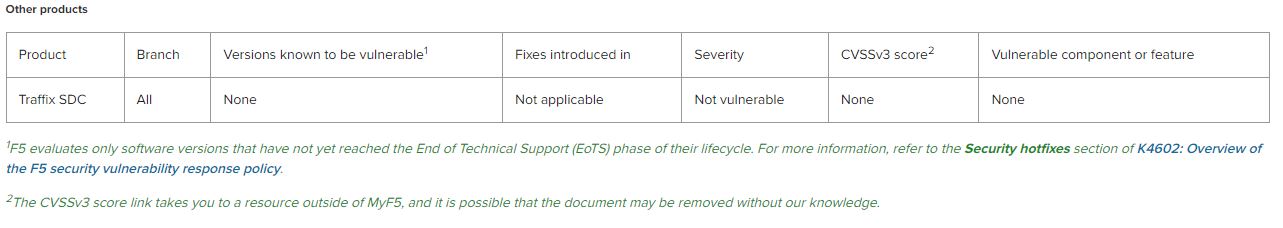
To determine if your product and version have been evaluated for this vulnerability, refer to the Evaluated products box. To determine if your release is known to be vulnerable, the components or features that are affected by the vulnerability, and for information about releases, point releases, or hotfixes that address the vulnerability, refer to the following tables. You can also use iHealth to diagnose a vulnerability for BIG-IP and BIG-IQ systems. For more information about using iHealth, refer to K27404821: Using F5 iHealth to diagnose vulnerabilities. For more information about security advisory versioning, refer to K51812227: Understanding security advisory versioning.
In this section:
BIG-IP and BIG-IQ
F5OS
NGINX
Other products
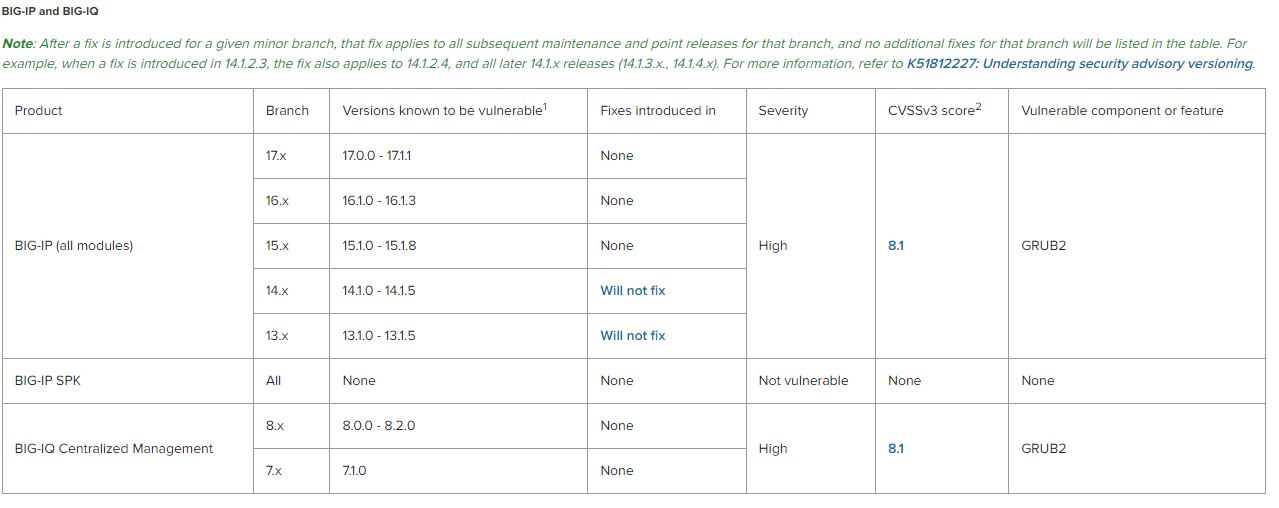
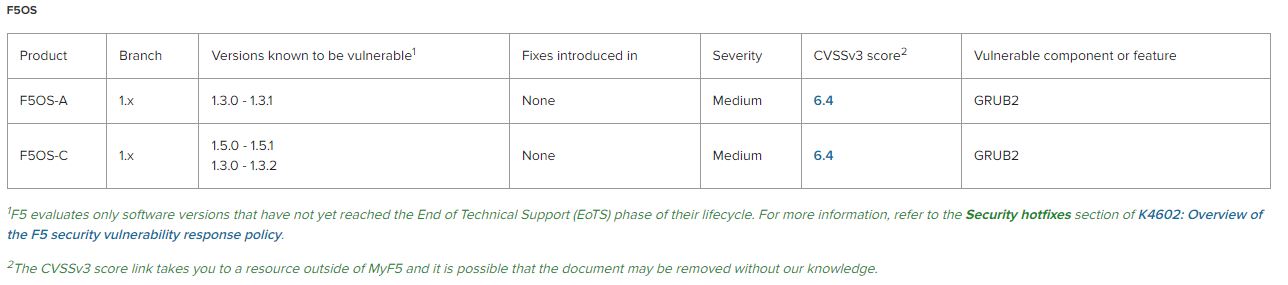
If you are running a version listed in the Versions known to be vulnerable column, you can eliminate this vulnerability by installing a version listed in the Fixes introduced in column. If the Fixes introduced in column does not list a version for your branch, then no update candidate currently exists for that branch and F5 recommends that you upgrade to a version with the fix (refer to the tables).
If the Fixes introduced in column lists a version prior to the one you are running, in the same branch, then your version should have the fix.
Mitigation:
To mitigate this vulnerability for affected F5 products, you should restrict management access to F5 products to only trusted users and devices over a secure network.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














