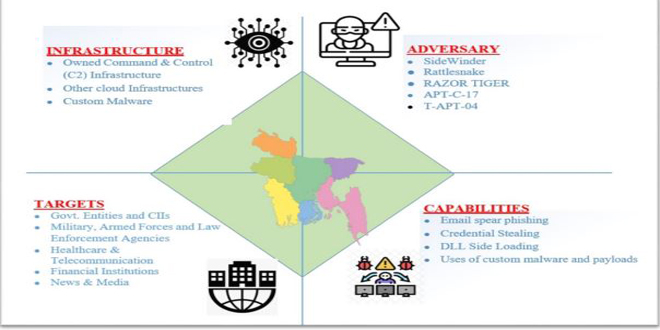
Cyber Threat Intelligence Unit of BGD e-GOV CIRT has detected a suspicious ongoing phishing campaign by APT group named as SideWinder targeted at Bangladeshi entities such as Bangladesh Armed Forces Division (AFD) and Law Enforcement Agencies.
The group is known as a highly active hacker group who has shown the capability to conductseveral attacks within a short time span and poses threats to organizations in South and East Asia. This alert includes an extensive list of IOCs and the group TTPs in order to help Bangladeshi organizations in taking preventive security measures accordingly. In Primary investigation we noticed that the main target of this APT group is to steal sensitive, confidential and classified documents.
The phishing campaign is done by a group called ‘Sidewinder’. This group has been operating since 2012 and is known for targeting government, military, and business entities in countries like Pakistan, China, Nepal, and more in Asia. They mainly use spear phishing attacks to gain unauthorized access to their targets.
Threat motives:
Sensitive, Confidential and Classified information theft and cyber espionage.
Target Sectors:
Government, Military, Law enforcement, HealthCare, Telecommunication, Financial Institutions, News and Media
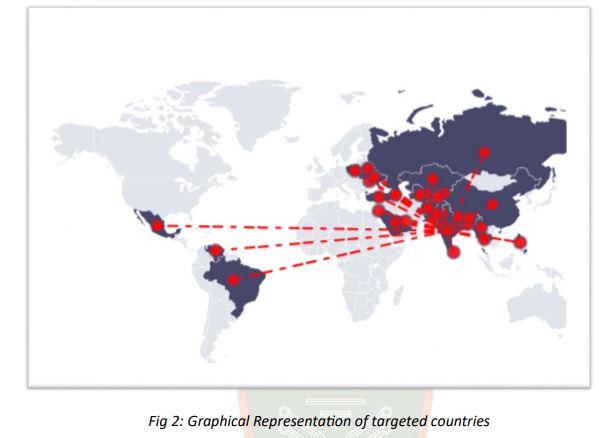
Target Countries:
Afghanistan, Armenia, China, Bangladesh, Belarus, Bhutan, Brazil, China, India, Israel, Kazakhstan, Kyrgyzstan, Mexico, Moldova, Myanmar, Nepal, Pakistan, Philippines, Poland, Qatar, Russian Federation, Saudi Arabia, Singapore, Sri Lanka, Tajikistan, Thailand, Turkey, Turkmenistan, Ukraine, Uzbekistan
SideWinder’s Cyberattack Chain:
“CIRT identified the attack process executed by the threat actor in various stages.”
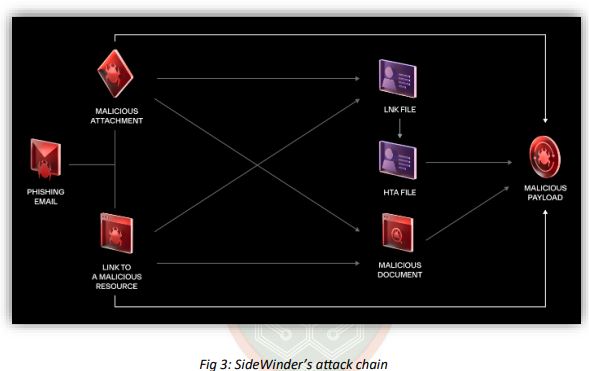
Initial access vector:
SideWinder uses spear phishing to target their victims. The attack starts with the victim receiving a fake email containing a harmful attachment or URL. The emails are made to look like they are from organizations the victims are affiliated with and appear to be related to their interests. They used domain names resembling those of government, military, and law enforcement agencies in Bangladesh. For example, cirt-gov-bd.donwloaded[.]com.
Code execution:
* When a user clicks on the malicious link/attached file (RTF, DOCX, ZIP, LNK,..etc.), a code execution is initiated to download a remote HTA file from the group’s controlled server.
* The HTA file run leads to the execution of the payload malware through DLL side
loading technique. (The malware can be a remote access Trojan (RAT) or an
information stealer)
* The Malware starts collecting sensitive and confidential info./files and send it to the
C2 server.
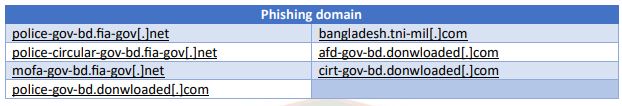
Phishing Domains:
BGD e-GOV CIRT’s Cyber Threat Intelligence Unit has found several phishing domains that imitate official websites and domains in Bangladesh. These domains are being used in an ongoing phishing campaign against entities in the country. The investigation has revealed that the domains, hash files, and IP addresses are associated with the SideWinder APT group. This group specifically targets government and law enforcement organizations in Bangladesh. Here are some of the phishing domains that have been identified:
To prevent malware execution following phishing attacks CIRT indicate some ways to be followed. Using denylists to block known malicious domains, URLs, and IP addresses as well as file extensions such as .scr, .exe, .pif, and .cpl and mislabeled file extensions (e.g., a .exe file that is labeled as a .doc file. Users must be restricted having adminstrative rights of MacOS and Windows. CIRT urges to implement the principle of least privilege (PoLP) when administering user accounts and to block macros by default.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind