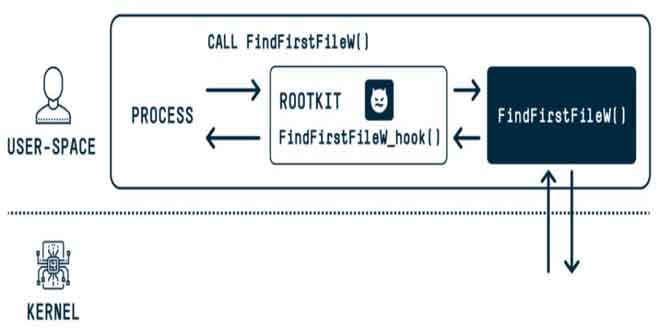
According to a new research bad actors could exploit the DOS-to-NT path conversion process to hide and impersonate files, directories, and processes, gaining rootkit-like capabilities.
“When a user executes a function that has a path argument in Windows, the DOS path at which the file or folder exists is converted to an NT path,” SafeBreach security researcher Or Yair said in an analysis, which was presented at the Black Hat Asia conference last week.
“During this conversion process, a known issue exists in which the function removes trailing dots from any path element and any trailing spaces from the last path element. This action is completed by most user-space APIs in Windows.”
The hackernews reported these so-called MagicDot paths allow for rootkit-like functionality that’s accessible to any unprivileged user, who could then weaponize them to carry out a series of malicious actions without having admin permissions and remain undetected.
They include the ability to “hide files and processes, hide files in archives, affect prefetch file analysis, make Task Manager and Process Explorer users think a malware file was a verified executable published by Microsoft, disable Process Explorer with a denial of service (DoS) vulnerability, and more.”
The discovery of four security shortcomings, three of which have since been addressed by Microsoft –
- An elevation of privilege (EoP) deletion vulnerability to delete files without sufficient privileges (to be fixed in a future release)
- An elevation of privilege (EoP) write vulnerability that allows unauthorized writing into files during the restoration process of a previous version (CVE-2023-32054, CVSS score: 7.3)
- A vulnerability that allows for remote code execution (RCE) by extracting a specially crafted archive (CVE-2023-36396, CVSS score: 7.8)
- A denial-of-service (DoS) vulnerability impacting Process Explorer when launching a lengthy executable name without a file extension
“This research is the first of its kind to explore how known issues that appear to be harmless can be exploited to develop vulnerabilities and, ultimately, pose a significant security risk,” Yair explained.
Rootkit-Like Powers:
“We believe the implications are relevant not only to Microsoft Windows, which is the world’s most widely used desktop OS, but also to all software vendors, most of whom also allow known issues to persist from version to version of their software.”
Source: SafeBreach, Thehackernews
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind