AMD has released a security bulletin about three possible vulnerabilities in its Secure Encrypted Virtualization – Secure Nested Paging (SEV-SNP) technology.
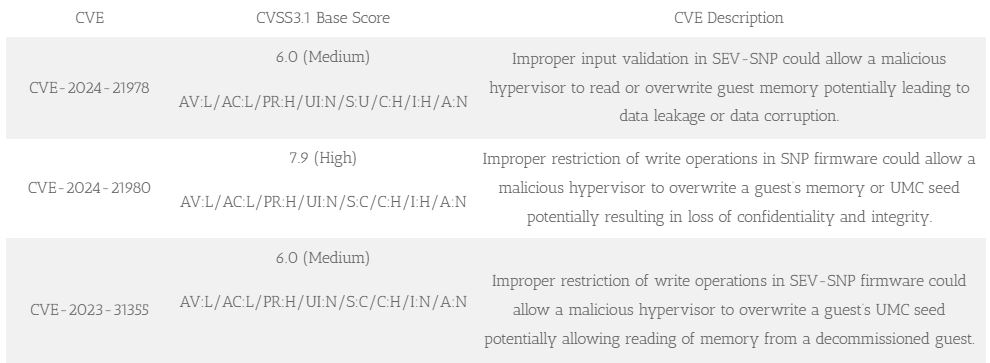
A researcher found vulnerabilities that could let a malicious hypervisor controlled by the host system access or modify the memory of a guest VM. This poses big risks to data security. The vulnerabilities are known as CVE-2024-21978, CVE-2024-21980, and CVE-2023-31355, with two rated as medium severity and one as high.
By infosecbulletin
/ Tuesday , September 16 2025
Cross-Site Scripting (XSS) is one of the oldest and most persistent vulnerabilities in modern applications. Despite being recognized for over...
Read More
By infosecbulletin
/ Monday , September 15 2025
Every day a lot of cyberattack happen around the world including ransomware, Malware attack, data breaches, website defacement and so...
Read More
By infosecbulletin
/ Monday , September 15 2025
A critical permission misconfiguration in the IBM QRadar Security Information and Event Management (SIEM) platform could allow local privileged users...
Read More
By infosecbulletin
/ Monday , September 15 2025
Australian banks are now using bots to combat scammers. These bots mimic potential victims to gather real-time information and drain...
Read More
By infosecbulletin
/ Saturday , September 13 2025
F5 plans to acquire CalypsoAI, which offers adaptive AI security solutions. CalypsoAI's technology will be added to F5's Application Delivery...
Read More
By infosecbulletin
/ Saturday , September 13 2025
The Villager framework, an AI-powered penetration testing tool, integrates Kali Linux tools with DeepSeek AI to automate cyber attack processes....
Read More
By infosecbulletin
/ Saturday , September 13 2025
Samsung released its monthly Android security updates, addressing a vulnerability exploited in zero-day attacks. CVE-2025-21043 (CVSS score: 8.8) is a...
Read More
By infosecbulletin
/ Saturday , September 13 2025
Albania has appointed the first AI-generated government minister to help eliminate corruption. Diella, the digital assistant meaning Sun, has been...
Read More
By infosecbulletin
/ Thursday , September 11 2025
On September 1, 2025, Qrator Lab identified and managed a major attack from the largest L7 DDoS botnet seen so...
Read More
By infosecbulletin
/ Thursday , September 11 2025
A new vulnerability, CVE-2025-4235, in Palo Alto Networks’ User-ID Credential Agent for Windows, could reveal a service account's password in...
Read More
SEV-SNP is a security feature for virtual machines that encrypts their memory to protect them from malicious attacks. However, vulnerabilities have been found in this feature due to issues with input validation and write operation restrictions in the firmware. These vulnerabilities could potentially allow a malicious hypervisor to access or corrupt a guest VM’s memory.
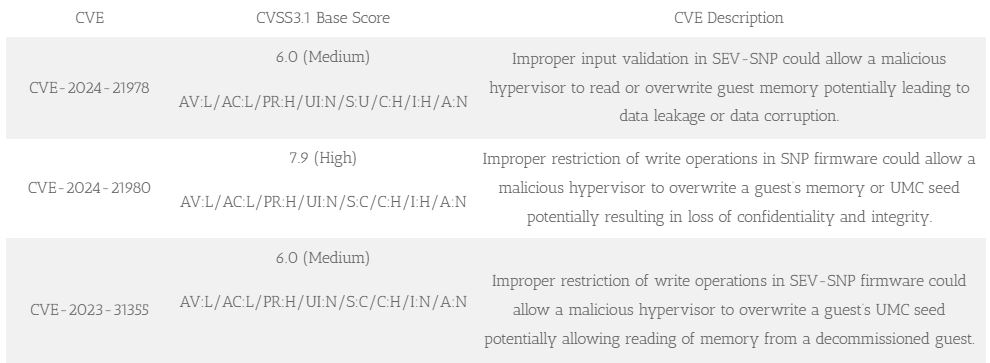
SEV-SNP firmware has a flaw that could let a malicious hypervisor overwrite a guest’s UMC seed, potentially allowing access to memory from a decommissioned guest.
These vulnerabilities are very important because they allow attackers to steal sensitive data, control VM operations, or even cause a denial of service. The affected products are AMD’s 3rd Gen EPYC Processors (Milan) and 4th Gen EPYC Processors (Genoa), which are commonly used in data centers and embedded systems.
To reduce the risks, AMD suggests that users update their systems with the latest Platform Initialization (PI) firmware versions mentioned in the advisory. In certain cases, there may be other options available for reducing the risks, like microcode or other patches.
For more information about firmware updates and how to protect your computer, please check the official AMD security bulletin and follow the guidelines.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














