AMD has released a security bulletin about three possible vulnerabilities in its Secure Encrypted Virtualization – Secure Nested Paging (SEV-SNP) technology.
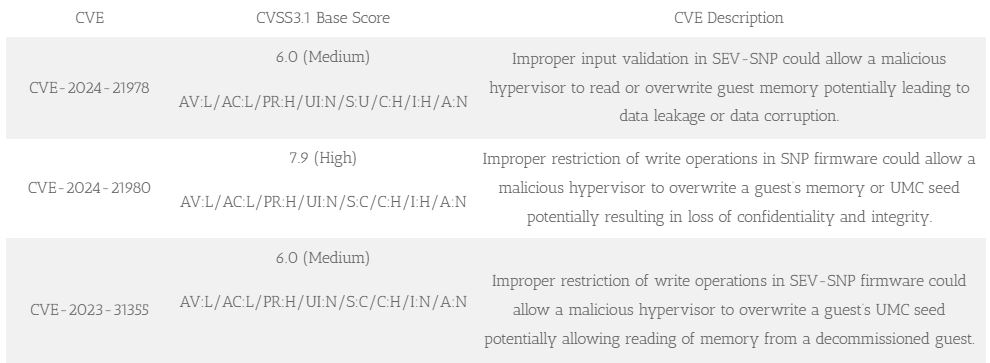
A researcher found vulnerabilities that could let a malicious hypervisor controlled by the host system access or modify the memory of a guest VM. This poses big risks to data security. The vulnerabilities are known as CVE-2024-21978, CVE-2024-21980, and CVE-2023-31355, with two rated as medium severity and one as high.
By infosecbulletin
/ Sunday , June 29 2025
Doctors at Columbia University Fertility Center have reported what they are calling the first pregnancy using a new AI system,...
Read More
By infosecbulletin
/ Saturday , June 28 2025
Cybersecurity experts and federal authorities are warning that the Scattered Spider hackers are now targeting aviation and transportation, indicating a...
Read More
By F2
/ Saturday , June 28 2025
Since June 9, 2025, Russian users connecting to Cloudflare services have faced throttling by ISPs. As the throttling is being...
Read More
By infosecbulletin
/ Saturday , June 28 2025
A new report from SafetyDetectives reveals that hackers posted a massive 3.1GB dataset online, containing about 61 million records reportedly...
Read More
By infosecbulletin
/ Friday , June 27 2025
A 30-year-old robotics engineer from Chennai set off alarm bells in 11 states by allegedly sending hoax bomb threats. She...
Read More
By infosecbulletin
/ Friday , June 27 2025
Cisco has issued updates to fix two critical security vulnerabilities in Identity Services Engine (ISE) and ISE Passive Identity Connector...
Read More
By F2
/ Thursday , June 26 2025
CISA warns about a serious vulnerability in Fortinet FortiOS that threatens network security. CISA included CVE-2019-6693 in its Known Exploited...
Read More
By F2
/ Thursday , June 26 2025
Rapid7 has revealed serious vulnerabilities in multifunction printers (MFPs) from Brother, FUJIFILM, Ricoh, and Toshiba Tec Corporation. These findings, covering...
Read More
By infosecbulletin
/ Wednesday , June 25 2025
Citrix has issued security updates for a critical vulnerability in NetScaler ADC that has been actively exploited. The vulnerability CVE-2025-6543...
Read More
By F2
/ Wednesday , June 25 2025
SonicWall warned on Monday that unknown attackers have trojanized its SSL-VPN NetExtender application, tricking users into downloading it from fake...
Read More
SEV-SNP is a security feature for virtual machines that encrypts their memory to protect them from malicious attacks. However, vulnerabilities have been found in this feature due to issues with input validation and write operation restrictions in the firmware. These vulnerabilities could potentially allow a malicious hypervisor to access or corrupt a guest VM’s memory.
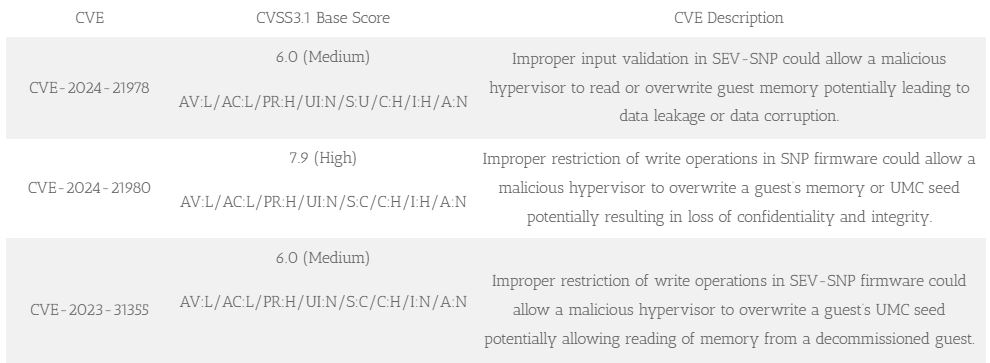
SEV-SNP firmware has a flaw that could let a malicious hypervisor overwrite a guest’s UMC seed, potentially allowing access to memory from a decommissioned guest.
These vulnerabilities are very important because they allow attackers to steal sensitive data, control VM operations, or even cause a denial of service. The affected products are AMD’s 3rd Gen EPYC Processors (Milan) and 4th Gen EPYC Processors (Genoa), which are commonly used in data centers and embedded systems.
To reduce the risks, AMD suggests that users update their systems with the latest Platform Initialization (PI) firmware versions mentioned in the advisory. In certain cases, there may be other options available for reducing the risks, like microcode or other patches.
For more information about firmware updates and how to protect your computer, please check the official AMD security bulletin and follow the guidelines.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














