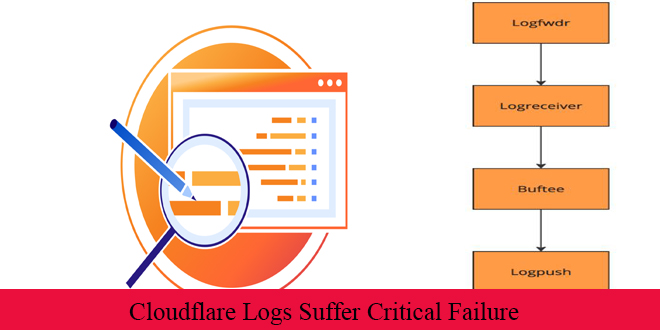
Cloudflare suffered an incident roughly 3.5 hours On November 14, 2024 impacting the majority of customers using Cloudflare Logs. Cloudflare lost about 55% of the logs normally send to customers were not sent and were lost on that incident.
Log services are crucial for network operations, helping businesses analyze traffic, troubleshoot issues, and detect threats. Cloudflare’s log service uses a tool called Logpush to process and deliver large amounts of data to customers.
By infosecbulletin
/ Monday , June 23 2025
A hacking group reportedly linked to Russian government has been discovered using a new phishing method that bypasses two-factor authentication...
Read More
By infosecbulletin
/ Wednesday , June 18 2025
Russian cybersecurity experts discovered the first local data theft attacks using a modified version of legitimate near field communication (NFC)...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
Cybersecurity researcher Jeremiah Fowler discovered an unsecured database with 170,360 records belonging to a real estate company. It contained personal...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
GreyNoise found attempts to exploit CVE-2023-28771, a vulnerability in Zyxel's IKE affecting UDP port 500. The attack centers around CVE-2023-28771,...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has recently included two high-risk vulnerabilities in its Known Exploited Vulnerabilities (KEV)...
Read More
By infosecbulletin
/ Monday , June 16 2025
SafetyDetectives’ Cybersecurity Team discovered a public post on a clear web forum in which a threat actor claimed to have...
Read More
By infosecbulletin
/ Sunday , June 15 2025
WestJet, Canada's second-largest airline, is looking into a cyberattack that has affected some internal systems during its response to the...
Read More
By infosecbulletin
/ Saturday , June 14 2025
Resecurity found 7.4 million records of Paraguayan citizens' personal information leaked on the dark web today. Last week, cybercriminals attempted...
Read More
By infosecbulletin
/ Friday , June 13 2025
HashiCorp has revealed a critical vulnerability in its Nomad tool that may let attackers gain higher privileges by misusing the...
Read More
By infosecbulletin
/ Friday , June 13 2025
SoftBank has disclosed that personal information of more than 137,000 mobile subscribers—covering names, addresses, and phone numbers—might have been leaked...
Read More
On November 14th, a Logpush update caused a significant error. Cloudflare’s incident report revealed that the update did not direct auxiliary tools to send the collected logs. Consequently, the logs were collected but never delivered and were eventually lost when the cache was cleared.
“A misconfiguration in one part of the system caused a cascading overload in another part of the system, which was itself misconfigured. Had it been properly configured, it could have prevented the loss of logs,” Cloudflare stated in their report.
Engineers team quickly found the flaw and reverted the update, but this caused a cascading failure. The system became overwhelmed with excessive log data, including from users who hadn’t set up Logpush, worsening the problem.
Cloudflare has apologized for the loss of user data and is implementing measures to prevent future incidents, though efforts are still underway.
The loss of important log data highlights the need for thorough testing and backup measures to maintain the integrity and availability of crucial information.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind