CISA has issued a critical alert about a critical vulnerability in Fortinet’s FortiOS and FortiProxy systems. CVE-2025-24472, an authentication bypass vulnerability, has been added to CISA’s Known Exploited Vulnerabilities catalog.
Fortinet FortiOS Authentication Bypass Vulnerability:
By infosecbulletin
/ Monday , June 23 2025
A hacking group reportedly linked to Russian government has been discovered using a new phishing method that bypasses two-factor authentication...
Read More
By infosecbulletin
/ Wednesday , June 18 2025
Russian cybersecurity experts discovered the first local data theft attacks using a modified version of legitimate near field communication (NFC)...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
Cybersecurity researcher Jeremiah Fowler discovered an unsecured database with 170,360 records belonging to a real estate company. It contained personal...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
GreyNoise found attempts to exploit CVE-2023-28771, a vulnerability in Zyxel's IKE affecting UDP port 500. The attack centers around CVE-2023-28771,...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has recently included two high-risk vulnerabilities in its Known Exploited Vulnerabilities (KEV)...
Read More
By infosecbulletin
/ Monday , June 16 2025
SafetyDetectives’ Cybersecurity Team discovered a public post on a clear web forum in which a threat actor claimed to have...
Read More
By infosecbulletin
/ Sunday , June 15 2025
WestJet, Canada's second-largest airline, is looking into a cyberattack that has affected some internal systems during its response to the...
Read More
By infosecbulletin
/ Saturday , June 14 2025
Resecurity found 7.4 million records of Paraguayan citizens' personal information leaked on the dark web today. Last week, cybercriminals attempted...
Read More
By infosecbulletin
/ Friday , June 13 2025
HashiCorp has revealed a critical vulnerability in its Nomad tool that may let attackers gain higher privileges by misusing the...
Read More
By infosecbulletin
/ Friday , June 13 2025
SoftBank has disclosed that personal information of more than 137,000 mobile subscribers—covering names, addresses, and phone numbers—might have been leaked...
Read More
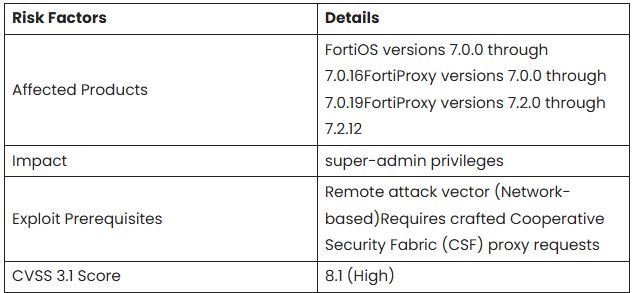
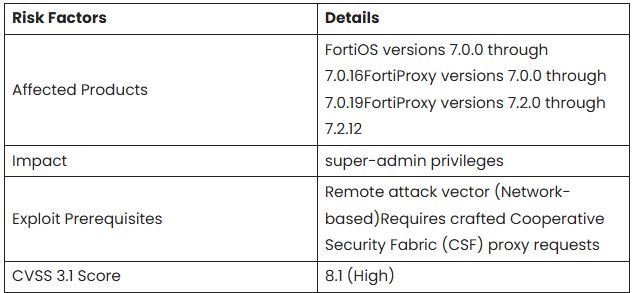
Fortinet FortiOS and FortiProxy contain an authentication bypass vulnerability that allows a remote attacker to gain super-admin privileges via crafted CSF proxy requests, which carries a CVSS score of 8.1.
The vulnerability affects FortiOS versions 7.0.0 to 7.0.16, FortiProxy 7.0.0 to 7.0.19, and FortiProxy 7.2.0 to 7.2.12.
Security experts caution that exploitation could give attackers full administrative access to systems, allowing them to create fake admin accounts, alter firewall policies, and reach SSL VPNs to access internal networks.
Mitigations:
CISA is directing organizations to “apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable”.
Fortinet has issued patches for vulnerabilities in FortiOS 7.0.17 and higher, as well as FortiProxy 7.0.20/7.2.13 and above.
The KEV catalog, managed by CISA, is a reliable source of known vulnerabilities actively exploited. CISA urges all organizations to prioritize fixing these Organizations should use the KEV catalog to prioritize their vulnerability management, as it is vital for effective external attack surface management and reducing compromise risks.
11 state hackers exploit new Windows zero-day since 2017
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














