Check point, a cyber security solutions provider hosts an event titled “securing the hyperconnected world in the AI era” at Dhaka today. 150+ participants from different sectors of Bangladesh including Bank, Telco, enterprise and so on attend the event.

The event was categorized in two parts including an engagement session and presentation where Abhishek Chakraborty, Regional Manager (North & East) India, Check Point and Md. Mahbubul Alam (Rafel), Head of Information Security Division, Prime Bank PLC interact each other.

In the very first engaging session, transform legacy system to digital, cohesiveness, remote work access risk and skill gap are discussed and find way out. They said, transforming legacy systems into digital platforms are crucial for organizations to remain competitive, but it presents challenges. Modernization improves efficiency and scalability, yet maintaining workflow cohesiveness is vital to prevent silos. Remote work has increased the need for secure access, raising risks like unauthorized access and data breaches. Organizations must enhance cybersecurity and adopt zero-trust models to address these threats. Additionally, the digital shift reveals a skill gap, as employees may lack knowledge in cloud, AI, or cybersecurity. Continuous training and upskilling are necessary to prepare the workforce for the future. Balancing technology, security, and people will be key to successful digital transformation.

In his presentation Abhishek Chakraborty, Regional Manager (North & East) India said, in 2025, AI is disrupting the threat landscape. Every single day the attack pattern is changing. So, organization must priorities cyber security as proactive manner.
Abhishek said, Edge device vulnerabilities are exploited as a main access vector to enterprise networks. Both state sponsored actors and financially motivated one’s target edge devices. In case of cloud, the attacker hijack cloud hosted LLM models where cloud administration complexity led to misconfiguration which leave organizations vulnerable.

To protect the organizations from such hybrid attack, he introduces the audiences check point’s “Infinity Platform” where Quantum for On- Premises Security, CloudGurad for Cloud Security and Harmony for Workspace Security is unified by Threatcloud AI.
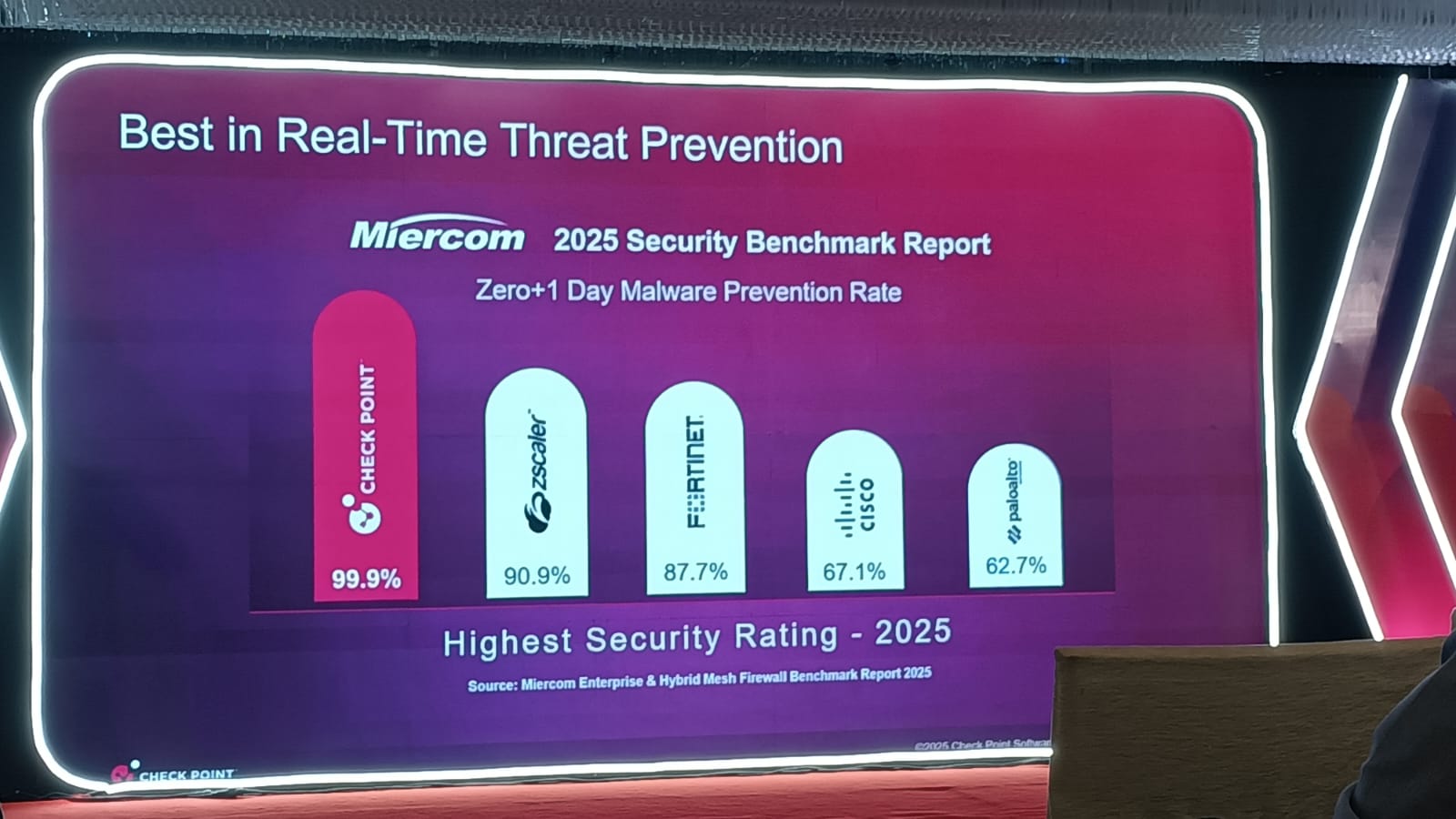
He said, in accordance with “Miercom Enterprise & Mess Firewall Benchmark Report -2025” with 99.9% malware prevention rate (Zero+ 1 day), Check point secured the best place for the real – time treat prevention.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














