Indian Computer Emergency Response Team (CERT-IN) issued advisories about multiple vulnerabilities in various Palo Alto Networks applications. Attackers could exploit these vulnerabilities to access systems without permission, steal important information, and potentially run harmful code.
Vulnerabilities in Palo Alto Networks:
The vulnerabilities include CVE-2024-5915, CVE-2024-5916, and CVE-2024-5914.
GlobalProtect App: Privilege Escalation Vulnerability (CVE-2024-5915):
Older versions of the Palo Alto Networks GlobalProtect app have a critical vulnerability. This vulnerability in the app on Windows devices allows a local user to run programs with higher privileges.
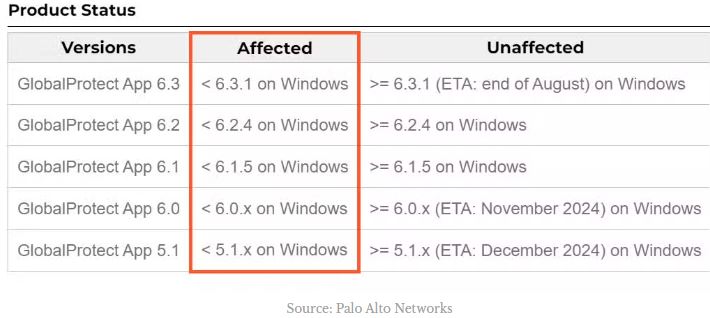
Users are advised to update your app to version 5.4.5 or higher to fix vulnerability CVE-2024-5915 and reduce the risk.
PAN-OS: Information Disclosure Vulnerability (CVE-2024-5916):
A new vulnerability, known as CVE-2024-5916, impacts Palo Alto Networks PAN-OS, a network security operating system. It’s classified as an “information exposure” problem.
If any attacker takes advantage of this vulnerability, they could get important information like passwords and tokens to access other systems. They could use this information to attack the network or compromise other systems.
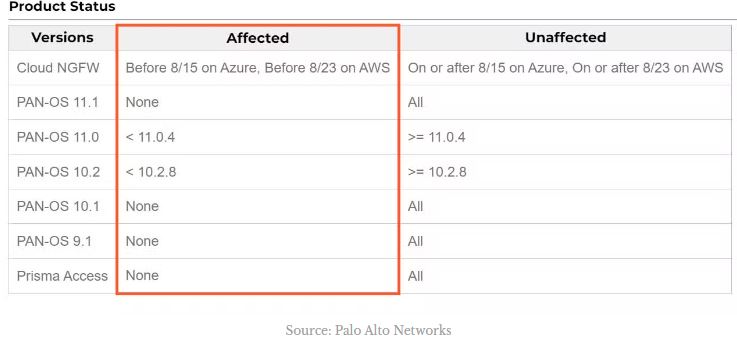
The vulnerability allows a read-only administrator to access sensitive details in the configuration log. This shows how important it is to give users the minimum access they need to do their tasks.
Resolution: The problem has been solved in PAN-OS 10.2.8, PAN-OS 11.0.4, and later versions. After upgrading PAN-OS, users should also revoke any compromised secrets, passwords, and tokens configured in server profiles (Device > Server Profiles) on affected PAN-OS firewalls.
Cortex XSOAR: Command Injection Vulnerability (CVE-2024-5914):
There is a vulnerability in older versions of Palo Alto Networks Cortex XSOAR. This vulnerability, known as CVE-2024-5914, is a “command injection” flaw in the CommonScripts Pack, which is a collection of scripts for automating security tasks.
Command injection vulnerabilities let attackers insert harmful code into trusted applications. In the case of Cortex XSOAR, if successfully exploited, attackers could run any command within an integration container. This could let attackers move within the network, steal data, or disrupt security operations.
Resolution:
Problem resolved in Cortex XSOAR CommonScripts v1.12.33+. Users are advised to update to the latest version to stay secure.
Protecting Against the Palo Alto Networks Vulnerabilities:
Palo Alto Networks has issued patches to fix these vulnerabilities. Users should update their software as soon as possible to reduce these risks.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind