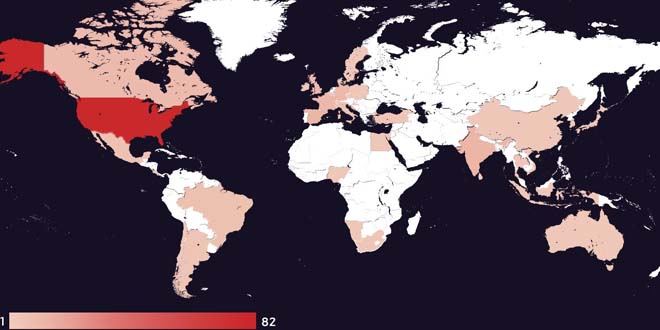
A cyber attack group from Indonesia has been allegedly targeting 12,000 government websites in India, according to a cybersecurity alert issued by the Centre.
The alert, accessed by Moneycontrol, was issued by the Ministry of Home Affairs’ Indian Cybercrime Coordination Centre (I4C) on Thursday.
Last year, a massive ransomware attack crippled the systems of All India Institute of Medical Science (AIIMS) rendering its centralised records inaccessible, apart from other hospital services.
Overall, the Indian government recorded 19 ransomware attacks against various government organisations in 2022, nearly three times the number recorded the previous year.
The I4C alert said that an Indonesian “hacktivist” group was launching denial of service (DoS) and distributed denial of service (DDoS) attacks. DDoS attacks refer to the intentional paralysing of a computer network by flooding it with data sent simultaneously from many individual computers.
The alert also said that the hacktivist group had released a list of government websites that it claims to be targeting, which included state and Central government websites.
“”Post this alert, government employees need to ensure that they do not fall for social engineering attacks; do not click on unknown emails or links, which can compromise security of such websites. They also ensure that all software updates are up-to-date,” Anand Prakash, founder and CEO of cybersecurity firm Pingsafe said.
Malaysian hacktivist group DragonForce targeted several Indian government websites including that of the Indian Embassy in Israel (indembassisrael[.]gov[.]in), National Institute of Agricultural Extension Management (manage[.]gov[.]in).
Govt’s guidelines to secure websites
Recently the government released the third version of Guidelines for India Government Websites (GIGW 3.0), which as the name suggests, provides guidelines to officials on how to safely, and securely, develop, maintain, and manage not just government websites, but also portals and mobile applications.
It recommended that developers should encrypt passwords, ensure software and plugins are up-to-date, connection strings, tokens, and keys. Website cookies should also be secure, it added.
It also urged developers to not give website backend access to too many high-level employees.
“Administrative privileges are given thinking those would be used carefully. Although this is the ideal situation, it is not always the case. Unfortunately, employees do not think about website security when logging into the Servers or the CMS,” the guidelines said.
“Instead, their thoughts are on the task at hand. If they make a mistake or overlook an issue, this can result in a significant security issue,” the GIGW 3.0 said, adding that it was vital to ensure employees have experience in handling back-end of websites before they gain access.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind