Cloudflare, despite its strong DDoS protection, can still be bypassed by exploiting logic flaws in its firewall demanded by Security researcher Stefan Proksch from Certitude. This allows attackers to perform DDoS attacks on targeted devices.
Cloudflare DDoS Protection Bypass Discovered:
Security researcher Stefan Proksch from Certitude recently discussed how an attacker can bypass Cloudflare’s DDoS protections by exploiting the service.
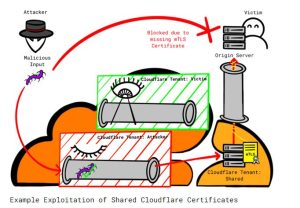
The researcher found two vulnerabilities in Cloudflare’s firewall and DDoS protection. The problems are related to how the service works, specifically with Cloudflare’s “Authenticated Origin Pulls” and “Allowlist Cloudflare IP Addresses.”
These mechanisms protect a server from harmful traffic by trusting HTTPS requests from Cloudflare. The service then verifies the traffic using an SSL/TLS certificate that customers can generate easily.
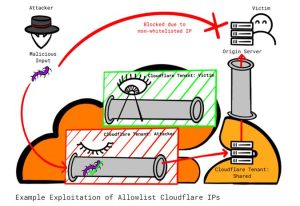
The researcher said that even though it seems reliable, allowing any Cloudflare traffic to be trusted could let someone use their own Cloudflare account to attack a particular server.The attacker only needs to know the IP address of the victim server to carry out the DDoS attack.
The researcher shared technical details and a proof of concept in his post. (Click here to see)
Official Patch Yet To Arrive:
Upon discovering the matter, the researcher responsible disclosed the vulnerability to Cloudflare via its HackerOne bug bounty program. However, after Cloudflare simply considered the report “informative,” the researcher decided on public disclosure. While the service hasn’t released an official patch to address the flaws yet, the researcher has suggested mitigations for the users.
Proksch suggests creating customized certificates using the “Authenticated Origin Pulls” feature instead of relying on Cloudflare certificates to prevent unauthorized requests. Additionally, he recommends using the “Allowlist Cloudflare IP addresses” feature as an additional layer of security, rather than relying on it as the only method of server protection.
Source:
certitude.consulting blog post
Bleeping computer
gb hacker
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














