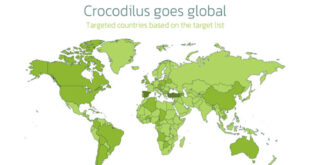
A new sophisticated scam is targeting Gmail users, using artificial intelligence to manipulate them into giving away account access. This “super realistic AI scam call” includes fake recovery notifications, spoofed phone numbers, and convincing AI voices to trick users.
The scam usually starts with an unexpected Gmail account recovery notification from a different country, according to a person named Sam who experienced it.
If ignored, scammers will call about 40 minutes later, often displaying caller ID like “Google Sydney” to seem legitimate.
AI Scam Call Flaw:
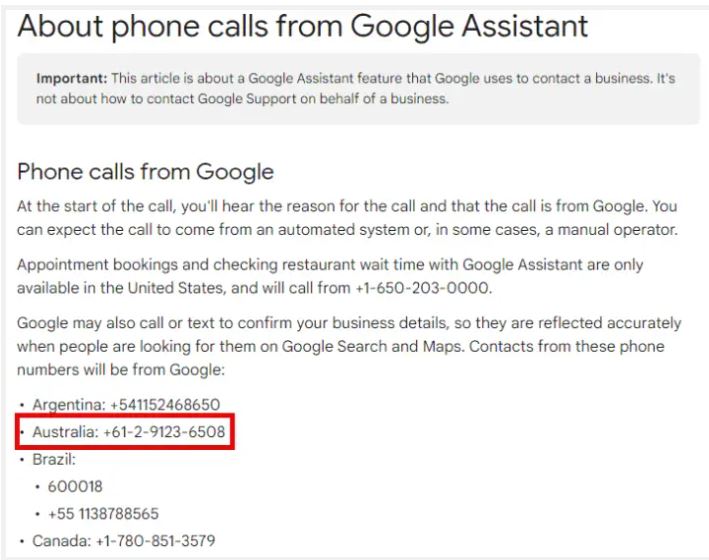
“I Googled the phone number, which led me to official Google documentation.The number seems legit although I’m aware just how easy it is to spoof the number”, Sam added.
When answered, an AI-generated voice with a convincing American accent claims to be from Google support.
Scammers impersonate a “representative” to alert users about suspicious account activity, often citing logins from foreign countries. They claim that someone accessed the account and downloaded personal data to create urgency. To make their claims seem credible, they send a fake email that looks like it’s from a Google domain, but closer examination shows signs of forgery, like non-Google email addresses in the “To” field.
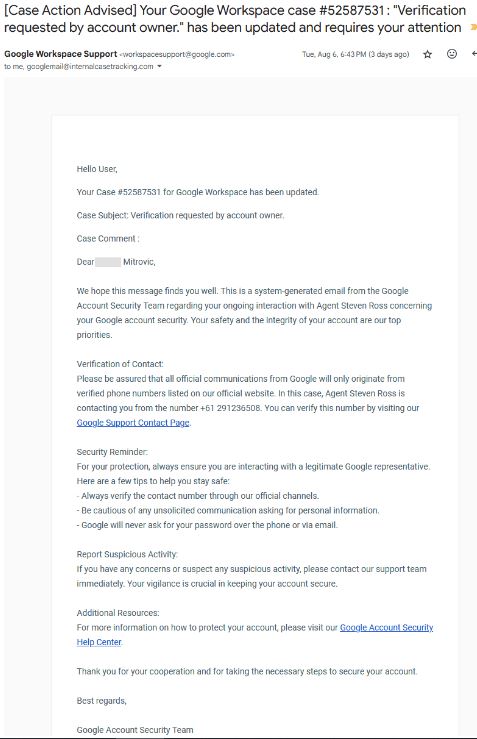
The goal is to get the victim to approve the initial account recovery request, which gives scammers full access to their Gmail. This access can lead to sensitive information theft, access to linked accounts, or further scams.
To Protect Yourself:
Never approve unexpected account recovery requests.
Be skeptical of unsolicited calls claiming to be from Google support.
Verify caller IDs and email addresses carefully.
Regularly check your account’s recent security activity.
When in doubt, contact Google directly through official channels.
As AI technology improves, scams are becoming more sophisticated. Stay vigilant and skeptical to avoid being a victim. If you suspect a scam, report it to Google and change your account passwords immediately.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind