Apple has released emergency security updates to address two new zero-day vulnerabilities exploited in attacks to compromise iPhones, Macs, and iPads.
“Apple is aware of a report that this issue may have been actively exploited,” the company said when describing the issues in security advisories published on Friday.
Successful exploitation allows attackers to use a maliciously crafted app to execute arbitrary code with kernel privileges on targeted devices.
The second zero-day (CVE-2023-28205) is a WebKit use after free weakness that allows data corruption or arbitrary code execution when reusing freed memory.
This flaw can be exploited by tricking the targets into loading malicious web pages under attackers’ control, which could lead to code execution on compromised systems.
The two zero-day vulnerabilities were addressed in iOS 16.4.1, iPadOS 16.4.1, macOS Ventura 13.3.1, and Safari 16.4.1 with improved input validation and memory management.
Apple says the list of affected devices is quite extensive, and it includes:
- iPhone 8 and later,
- iPad Pro (all models),
- iPad Air 3rd generation and later,
- iPad 5th generation and later,
- iPad mini 5th generation and later,
- and Macs running macOS Ventura.
Three zero-days patched since the start of the year
Even though Apple says it’s aware of in-the-wild exploitation reports, the company is yet to publish information regarding these attacks.
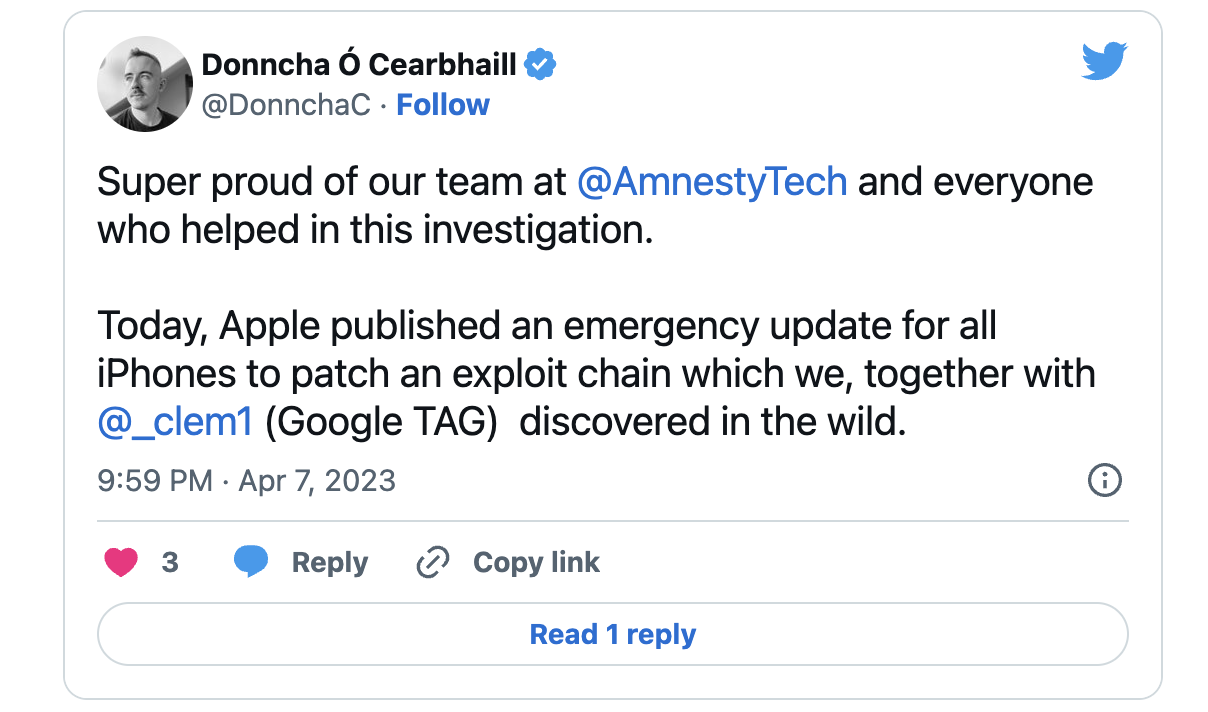
However, it revealed that the two flaws had been reported by Clément Lecigne of Google’s Threat Analysis Group and Donncha Ó Cearbhaill of Amnesty International’s Security Lab after finding them exploited in the wild as part of an exploit chain.
Both organizations regularly disclose campaigns exploiting zero-day bugs abused by government-sponsored threat actors to deploy commercial spyware on the smartphones and computers of politicians, journalists, dissidents, and other high-risk individuals worldwide.
Last week, Google TAG and Amnesty International exposed two recent series of attacks using exploit chains of Android, iOS, and Chrome zero-day and n-day flaws to deploy mercenary spyware.
While the zero-days patched today were most likely only used in highly-targeted attacks, installing these emergency updates as soon as possible is highly recommended to block potential attack attempts.
In February, Apple addressed another WebKit zero-day (CVE-2023-23529) exploited in attacks to trigger OS crashes and gain code execution on vulnerable iPhones, iPads, and Macs.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind