Following reports of a ransomware attack, Taiwanese PC vendor MSI (short for Micro-Star International) confirmed today that its network was breached in a cyberattack.
Earlier this week, the Money Message ransomware gang claimed to infiltrate some of MSI’s systems and stolen files that will be leaked online next week if the company refuses to pay a $4 million ransom.
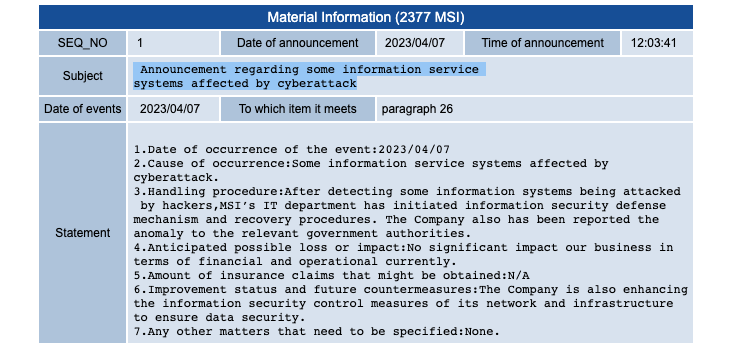
“After detecting some information systems being attacked by hackers, MSI’s IT department has initiated information security defense mechanism and recovery procedures. The Company also has been reported [sic] the anomaly to the relevant government authorities,” MSI said.
The company did not share any details on the timing of the attack, about if any of the affected systems were encrypted, or if the attackers exfiltrated business and customer information during the incident.
However, MSI did say that the cyberattack has had no “significant” operational and financial impact, with security enhancements implemented to ensure that data stored on affected systems is secure.
“No significant impact our business in terms of financial and operational currently. The Company is also enhancing the information security control measures of its network and infrastructure to ensure data security.”
MSI also published a statement on Friday warning customers to ensure that they get their BIOS and firmware updates from official sources.
“MSI urges users to obtain firmware/BIOS updates only from its official website, and not to use files from sources other than the official website,” the company said.
BleepingComputer first covered the Money Message ransomware operation’s activity in a report published last weekend after hearing of the group’s potential involvement in the breach of a high-profile computer hardware vendor.
According to chats seen by BleepingComputer between the ransomware gang and an MSI representative, the threat actors demanded a ransom payment of $4,000,000 based on a claim that they’ve stolen roughly 1.5TB worth of documents from MSI’s network.
Money Message now threatens to release the allegedly stolen files sometime next week if MSI fails to meet its ransom demands.
The threat actors have listed MSI on their data leak site, so far only sharing screenshots of what they describe as the PC maker’s Enterprise Resource Planning (ERP) databases and files containing software source code, private keys, and BIOS firmware.
MSI is yet to reply to multiple emails from BleepingComputer asking for a statement regarding the Money Message ransomware gang’s claims.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind