Cyber security organization “Enterprise Infosec Consultants (EIC)” of Bangladesh has become a member of CREST, an organization of various organizations working on cyber security around the world.
The membership was granted by the UK-based non-profit organization after reviewing the EIC’s capabilities in cyber security prevention. According to the Certificate provided by CREST, EIC meet the requirement for penetration testing.
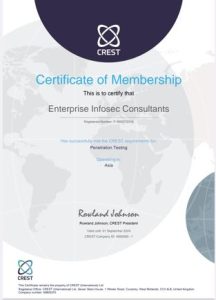
CREST is an international not-for-profit, membership body representing the global cyber security industry. Its goal is to help create a secure digital world for all by quality assuring our members and delivering professional certifications to the cyber security industry.
CREST accredit 300 member companies, operating across dozens of countries, and certify thousands of professionals worldwide. CREST works with governments, regulators, academe, training partners, professional bodies and other stakeholders around the world. Its members undergo a rigorous quality assurance process and employ competent professionals. Organizations buying their cyber security services from its members do so with confidence.
In accordance with CREST stated aim “to increase professionalism in the security testing industry”, it place requirements on member companies in order to ensure that consistent standards of services are delivered.
The requirements fall into 4 main areas:
Company operating procedures and standards
Personnel security and development
Approach to testing and response
Data security
Prior to applying to join, prospective member companies are encouraged to review the requirements documents and ascertain their compliance status.
Prospective Member Companies can apply for membership in any or all of the following disciplines:
Penetration Testing
Vulnerability Assessment
Intelligence-Led Penetration Testing (CREST STAR)
Threat Intelligence
STAR-FS
Cyber Security Incident Response
SOC
During the application process, CREST will require copies of the certain documents. These include:
General company details;
Copy of a professional indemnity insurance certificate or company letter confirming level professional indemnity insurance;
Contract management, including a copy of a sample contract with terms and conditions;
Policies and procedures relating to the use of contractors, including a copy of a sample contract with terms and conditions;
Copies of standards compliance certificates (e.g. ISO27001, ISO9001).
Quality processes and procedures;
Information Security processes and procedures;
Complaint Handling and Conflict of Interest policies.
Each discipline has its own separate application form where CREST will review specific methodologies for delivering the service you are applying for.
Chief Executive Officer of EIC Mashiul Islam said, Really CREST measures the international standardization of the company weather its meet or not and scrutinize audit, work flow, skill, compliance etc.
“I fell really honored to get this recognition as we have been providing cyber security to various organizations since 2016. And so this recognition is very happy for us.
He said, CREST certificate is considered important for foreign country penetration. We worked for 3 month to get this recognition with CREST.
It should be noted that CREST regularly reviews the work standards and procedures of member institutions to ensure international standard cyber security services. And so the member institutions of the organization get global acceptance.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind