AhnLab’s Security Emergency Response Center (ASEC) studies attacks on poorly secured Linux SSH servers and shares the findings on the ASEC Blog.
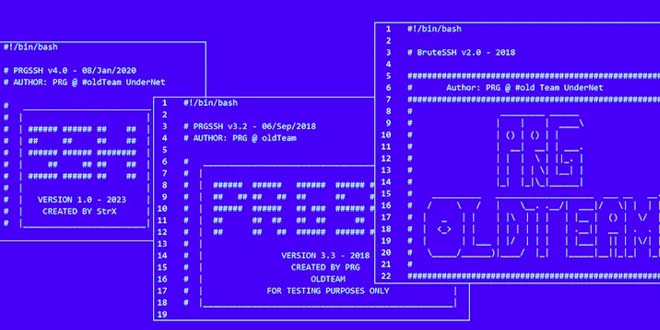
Attackers need to find out the IP address and SSH account details before installing malware like DDoS bot and CoinMiner. They scan for servers with the SSH service (port 22) activated to carry out brute force or dictionary attacks to get the login information.
By F2
/ Wednesday , July 2 2025
The second day of the Cyber Defence & Security Exhibition and Conference (CYDES) 2025 further cemented Malaysia’s position as a...
Read More
By F2
/ Tuesday , July 1 2025
Malaysia's Deputy Prime Minister Datuk Seri Dr. Ahmad Zahid Hamidi said that Malaysia has placed cybersecurity at the heart of...
Read More
By F2
/ Tuesday , July 1 2025
Mark Chen, the chief research officer at OpenAI, sent a forceful memo to staff on Saturday, promising to go head-to-head...
Read More
By F2
/ Tuesday , July 1 2025
The Canadian government ordered Hikvision to stop all operations in the country due to national security concerns. Hikvision, based in...
Read More
By infosecbulletin
/ Sunday , June 29 2025
Doctors at Columbia University Fertility Center have reported what they are calling the first pregnancy using a new AI system,...
Read More
By infosecbulletin
/ Saturday , June 28 2025
Cybersecurity experts and federal authorities are warning that the Scattered Spider hackers are now targeting aviation and transportation, indicating a...
Read More
By F2
/ Saturday , June 28 2025
Since June 9, 2025, Russian users connecting to Cloudflare services have faced throttling by ISPs. As the throttling is being...
Read More
By infosecbulletin
/ Saturday , June 28 2025
A new report from SafetyDetectives reveals that hackers posted a massive 3.1GB dataset online, containing about 61 million records reportedly...
Read More
By infosecbulletin
/ Friday , June 27 2025
A 30-year-old robotics engineer from Chennai set off alarm bells in 11 states by allegedly sending hoax bomb threats. She...
Read More
By infosecbulletin
/ Friday , June 27 2025
Cisco has issued updates to fix two critical security vulnerabilities in Identity Services Engine (ISE) and ISE Passive Identity Connector...
Read More
ALSO READ:
Barracuda fixes new ESG zero-day exploited by hackers
Threat actors gain more cryptocurrency by controlling more CoinMiners. They also have the ability to launch stronger DDoS attacks by controlling more DDoS bots. However, in order to increase the number of CoinMiners and DDoS bots, they need to gather more information or account credentials from their targets.
In addition to DDoS bots and CoinMiners, attackers can also install malware to perform scanning and brute force or dictionary attacks on infected systems, allowing them to take advantage of more vulnerable systems. Attackers can also just install scanners and sell the breached IP and account credentials on the dark web.
Poorly managed SSH servers can become targets for various types of malware, including SSH scanner, DDoS bots, and CoinMiners. This post analyzes cases of attacks involving these malware.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind