In today’s changing cybersecurity environment, it’s essential to find vulnerabilities in code. Vulnhuntr, an open-source tool on GitHub, uses Large Language Models (LLMs) and static code analysis to detect remotely exploitable vulnerabilities in Python projects. Its user-friendly design combines intelligent automation with thorough code analysis, making it a valuable resource for developers and security professionals.
How Vulnhuntr Works:
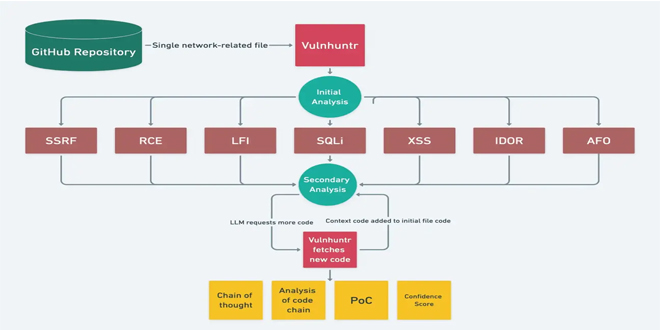
Vulnhuntr employs a unique multi-stage approach to vulnerability detection:
LLM-Powered README Analysis: The LLM starts by examining the project’s README file to understand the codebase’s functions and potential vulnerabilities, which informs further analysis.
Initial Code Scan: The LLM checks the whole codebase for potential security issues based on its knowledge of secure coding and common vulnerabilities.
Contextual Deep Dive: Vulnhuntr gives the LLM a specific prompt for each potential vulnerability, prompting a deeper analysis. The LLM asks for more context from related files, tracking data flow from user input to server processing. This helps identify vulnerabilities across multiple files and functions.
Comprehensive Vulnerability Report: Vulnhuntr generates a detailed report outlining its findings. This report includes:
Initial assessment results for each file
Secondary assessment results with context functions and class references
Confidence scores for each vulnerability
Logs of the analysis process
Proof-of-concept (PoC) exploits for validated vulnerabilities
Example Vulnerabilities Found in Repositories
In its recent scans, Vulnhuntr has uncovered vulnerabilities in several high-profile projects, showcasing its effectiveness:
gpt_academic (64k stars): LFI, XSS
ComfyUI (50k stars): XSS
FastChat (35k stars): SSRF
REDACTED (29k stars): RCE, IDOR
Ragflow (16k stars): RCE
These findings show the variety of vulnerabilities Vulnhuntr can find, ranging from LFI in research tools to RCE in machine learning projects.
Limitations:
While Vulnhuntr represents a significant advancement in vulnerability scanning, it has some limitations:
Python Support: Currently, the tool only supports Python codebases.
Vulnerability Classes: Vulnhuntr can identify a specific set of vulnerability classes, including LFI, AFO, RCE, XSS, SQLI, SSRF, and IDOR.
Vulnhuntr combines LLMs with static code analysis for a new approach to vulnerability detection. It offers both high-level and detailed insights, dynamically gathering context from related code parts for thorough coverage. Its final analysis includes PoC exploits and confidence scores, providing actionable information for developers and security teams.
You can explore Vulnhuntr and contribute to its development on GitHub.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind