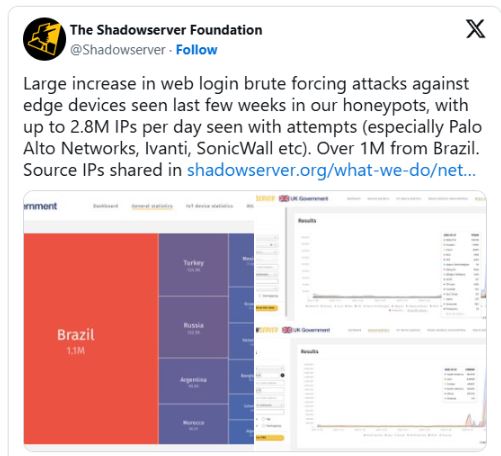
The Shadowserver Foundation reports that a brute force attack has been active since last month, using nearly 2.8 million IP addresses each day attempting to guess the credentials for a wide range of networking devices.
A brute force attack occurs when attackers repeatedly try different usernames and passwords to access an account or device until they find the right combination. Once they gain access, they can hijack the device or network.
By F2
/ Tuesday , June 24 2025
The U.S. House of Representatives has banned congressional staff from using WhatsApp on government devices due to security concerns, as...
Read More
By F2
/ Tuesday , June 24 2025
Kaspersky found a new mobile malware dubbed SparkKitty in Google Play and Apple App Store apps, targeting Android and iOS....
Read More
By F2
/ Tuesday , June 24 2025
OWASP has released its AI Testing Guide, a framework to help organizations find and fix vulnerabilities specific to AI systems....
Read More
By F2
/ Tuesday , June 24 2025
In a major milestone for the country’s digital infrastructure, Axentec PLC has officially launched Axentec Cloud, Bangladesh’s first Tier-4 cloud...
Read More
By infosecbulletin
/ Monday , June 23 2025
A hacking group reportedly linked to Russian government has been discovered using a new phishing method that bypasses two-factor authentication...
Read More
By infosecbulletin
/ Wednesday , June 18 2025
Russian cybersecurity experts discovered the first local data theft attacks using a modified version of legitimate near field communication (NFC)...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
Cybersecurity researcher Jeremiah Fowler discovered an unsecured database with 170,360 records belonging to a real estate company. It contained personal...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
GreyNoise found attempts to exploit CVE-2023-28771, a vulnerability in Zyxel's IKE affecting UDP port 500. The attack centers around CVE-2023-28771,...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has recently included two high-risk vulnerabilities in its Known Exploited Vulnerabilities (KEV)...
Read More
By infosecbulletin
/ Monday , June 16 2025
SafetyDetectives’ Cybersecurity Team discovered a public post on a clear web forum in which a threat actor claimed to have...
Read More
The majority of the 1.1 million participants come from Brazil, followed by Turkey, Russia, Argentina, Morocco, and Mexico with many other as source of origin.
These are security devices like firewalls, VPNs, and gateways that are often connected to the internet for remote access.
The attacks mostly involve compromised MikroTik, Huawei, Cisco, Boa, and ZTE routers and IoT devices, often controlled by large malware botnets.
BleepingComputer reports that the Shadowserver Foundation has confirmed that this activity has been ongoing for some time but has recently intensified significantly.
ShadowServer reported that the attacking IP addresses come from various networks and Autonomous Systems, suggesting they may be part of a botnet or linked to residential proxy networks.
To protect edge devices from brute-force attacks, change the default admin password to a strong, unique one, enable multi-factor authentication (MFA), use an allowlist of trusted IPs, and disable unnecessary web admin interfaces.
U.K. orders Apple to let it spy on users’ encrypted accounts: Report
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














