Mikhail Pavlovich Matveev, a 30-year-old Russian national, has been charged by the US Justice Department for his alleged role in numerous ransomware attacks, including ones targeting critical infrastructure.
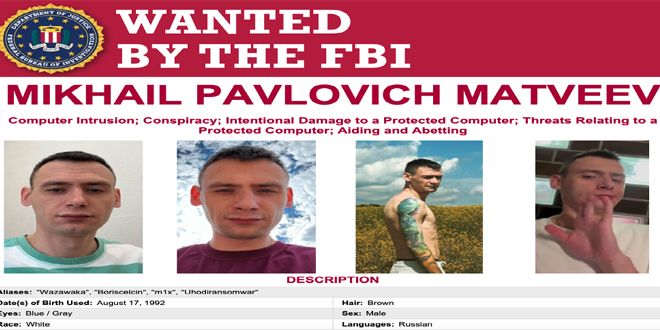
Matveev — known online as Wazawaka, m1x, Boriselcin, and Uhodiransomwar — has been charged with conspiring to transmit ransom demands, conspiring to damage protected computers, and intentionally damaging protected computers.
He faces over 20 years in prison, but he is unlikely to be arrested and convicted any time soon considering that he is believed to be living in Russia. While law enforcement cooperation between Russia and the US seemed to be improving before the start of the Ukraine war, it’s unlikely that Russia will hand over any cybercriminals to the United States given their current relations.
According to the US Justice Department, Matveev has been affiliated with several major ransomware operations, including LockBit, Hive and Babuk. He and other members of these operations allegedly targeted thousands of entities in the United States and elsewhere, including hospitals, schools, airlines, businesses, law enforcement, and other government organizations.
The specific examples shared by authorities include the LockBit attack on a Passaic County (NJ) police department, a Hive attack on a healthcare organization in Mercer County (NJ), and a Babuk attack on the Washington DC Metropolitan Police Department.
Prosecutors pointed out that the three ransomware operations in which Matveev was involved demanded as much as $400 million from their victims, and they are believed to have received up to $200 million.
Matveev was revealed to be Wazawaka by Brian Krebs in early 2022, which the Russian confirmed shortly after. In August 2022, he gave an interview to The Record in which — using his real name — detailed his hacking activities.
In addition to the charges brought against him, Matveev has been added to the FBI’s Most Wanted list, and the Treasury Department announced sanctions against him. The Department of State announced that it’s prepared to award up to $10 million for information that leads to the man’s arrest.
The LockBit ransomware operation continues to be highly active, but Hive has been shut down by law enforcement. In the case of Babuk, its source code was leaked in 2021, which has led to the creation of several new ransomware families.
The FBI described Matveev as one of the “developers/administrators behind the Babuk ransomware variant”.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind