Sekoia.io and Intrinsec analyzed the Quad7 (7777) botnet, which uses TCP port 7777 on infected routers to carry out brute-force attacks on Microsoft 365 accounts. Attacks were detected on 0.11% of monitored accounts.
Key insights highlighted by researchers:
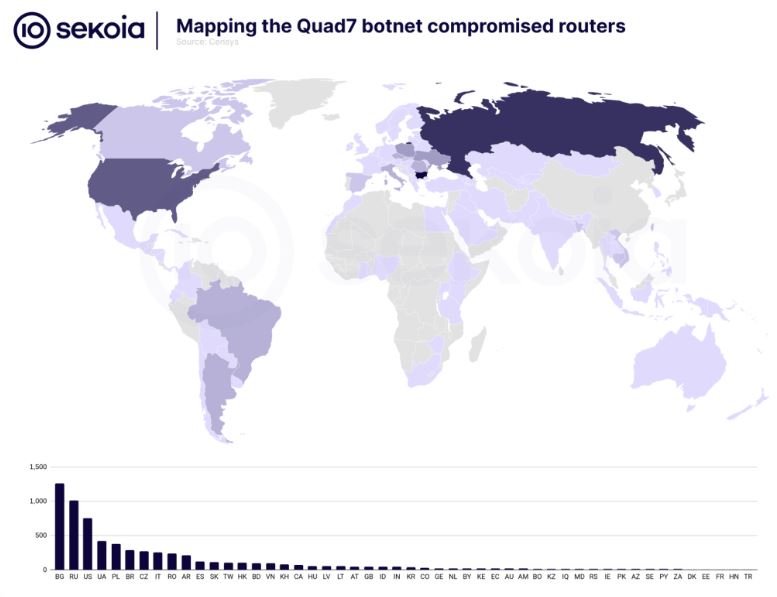
Botnet Evolution: Quad7 has been active for a long time and continues to evolve. The number of unique IP addresses has decreased from 16,000 in August 2022 to 7,000 in July 2024. The highest number of infected devices are in Bulgaria, Russia, the USA, and Ukraine.
Botnet Targets: Quad7 targets various IoT devices, including IP cameras, NAS devices, and SOHO routers, primarily TP-Link.
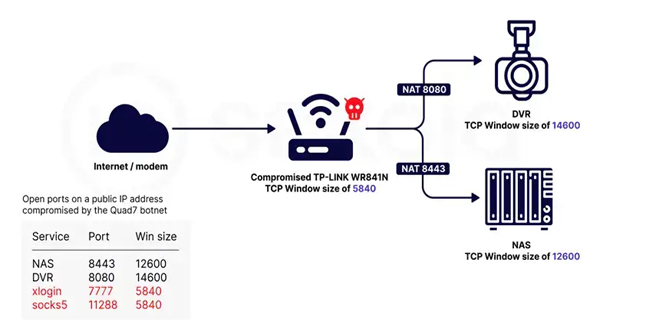
TP-Link Detection: Botnet operators disable the TP-Link management interface after compromise, making detection difficult. Researchers used the hping3 tool and found that most devices have a TCP window size characteristic of older Linux kernel versions used in TP-Link routers.
Researchers observed a TP-Link WR841N router with insecure firmware that allowed access from five different IP addresses. Experts set up remote analysis and utilized the Scapy library to monitor authentication attempts.
After observing for several days, an attack happened when the attacker used a weakness to access files and run code. The hacker used Dropbear on a different port and sent a utility package through an SSH connection. They also stopped the web interface and uploaded files to the router.
The Telnet binary listens on TCP/7777 and redirects incoming connections to a simple authenticated shell named xlogin. Additionally, a Socks5 proxy server listens on SOCKS/11288, through which brute force attacks on Microsoft 365 accounts are conducted.
The Quad7 botnet is targeting Microsoft 365 accounts with Password Spraying attacks. It connects to servers for IP address verification and binary file updates. Important questions about the attacks, vulnerabilities, and botnet’s geographical distribution remain unanswered. Researchers at Sekoia.io ask companies with a wider perspective for help in solving these mysteries.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind