Security researchers have released a proof-of-concept exploit for CVE-2025-20029, a serious command injection vulnerability in F5’s BIG-IP application delivery controllers.
The flaw has a CVSS v3.1 score of 8.8 and allows authenticated attackers to execute arbitrary system commands due to improper handling of special elements in the iControl REST API and TMOS Shell (tmsh).
Attackers can exploit vulnerabilities to gain root-level access from standard user privileges, jeopardizing the entire BIG-IP control plane.
The vulnerability arises from insufficient input sanitization in the tmsh command-line interface’s save functionality, where attackers can inject malicious parameters containing shell metacharacters like ; or &&.
This exploits F5’s limited command environment by mishandling user-supplied arguments in system() calls. Exploitation needs valid credentials, but it’s easy to execute because vulnerable command sequences are predictable.
Researchers showed that attackers can use stolen credentials along with this vulnerability to run reconnaissance commands, write malicious files to /var/tmp, and escalate privileges by injecting cron jobs.
Proof-of-Concept Exploit Mechanics:
The released PoC leverages BIG-IP’s REST API endpoint /mgmt/tm/util/bash to bypass command restrictions. A crafted JSON payload exploits the improper argument handling in the configuration backup process.
Successful execution returns a 200 OK response while running injected commands with root privileges.
Analysts confirm the exploit chain can:
Extract administrative credentials from /config/bigip.license
Modify iRule configurations to establish persistent backdoors
Disrupt traffic management policies through tmsh delete operations
Mitigation Strategies:
Temporary mitigations include:
Restricting iControl REST access via port lockdown settings on self-IPs.
Implementing network segmentation for management interfaces.
Enforcing strict RBAC policies to limit tmsh command availability.
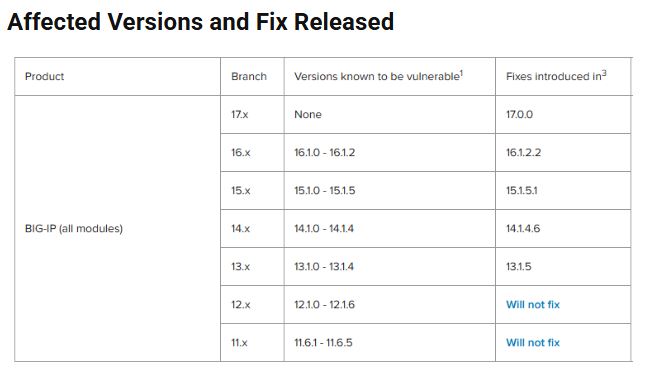
CVE-2025-20029 represents a critical infrastructure threat requiring prioritized remediation.
Organizations should apply F5’s security updates within 24 hours, audit systems exposed to management interface traffic, and implement runtime application self-protection (RASP) rules to detect command injection.
As network appliances are targeted more often, the security community stresses the importance of strengthening API endpoints and using zero-trust principles for access management.
Source: GitHub, cybersecuritynews
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














