MANILA, Philippines —A staggering 1,279,437 records belonging to law enforcement agencies, including sensitive police employee information, have been compromised in an unprecedented data breach, as revealed by a report from the leading cybersecurity research company VPNMentor on Tuesday.
The massive data hack, which exposed 817.54 gigabytes of both applicant and employee records under multiple state agencies, including the Philippine National Police (PNP), National Bureau of Investigation (NBI), Bureau of Internal Revenue (BIR), and Special Action Force (SAF), has put the personal information of millions of Filipinos at risk.
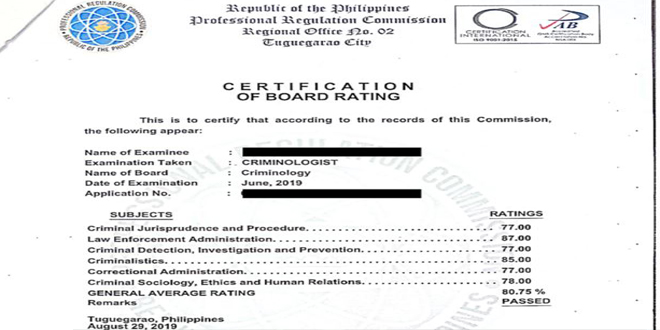
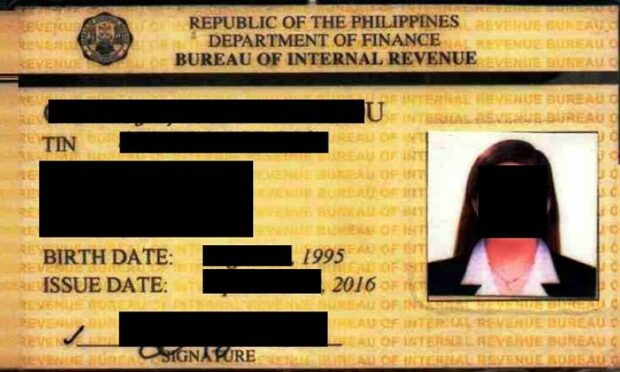
Exposed records encompass highly sensitive data such as fingerprint scans, birth certificates, tax identification numbers (TIN), tax filing records, academic transcripts, and even passport copies.
By infosecbulletin
/ Tuesday , September 16 2025
Cross-Site Scripting (XSS) is one of the oldest and most persistent vulnerabilities in modern applications. Despite being recognized for over...
Read More
By infosecbulletin
/ Monday , September 15 2025
Every day a lot of cyberattack happen around the world including ransomware, Malware attack, data breaches, website defacement and so...
Read More
By infosecbulletin
/ Monday , September 15 2025
A critical permission misconfiguration in the IBM QRadar Security Information and Event Management (SIEM) platform could allow local privileged users...
Read More
By infosecbulletin
/ Monday , September 15 2025
Australian banks are now using bots to combat scammers. These bots mimic potential victims to gather real-time information and drain...
Read More
By infosecbulletin
/ Saturday , September 13 2025
F5 plans to acquire CalypsoAI, which offers adaptive AI security solutions. CalypsoAI's technology will be added to F5's Application Delivery...
Read More
By infosecbulletin
/ Saturday , September 13 2025
The Villager framework, an AI-powered penetration testing tool, integrates Kali Linux tools with DeepSeek AI to automate cyber attack processes....
Read More
By infosecbulletin
/ Saturday , September 13 2025
Samsung released its monthly Android security updates, addressing a vulnerability exploited in zero-day attacks. CVE-2025-21043 (CVSS score: 8.8) is a...
Read More
By infosecbulletin
/ Saturday , September 13 2025
Albania has appointed the first AI-generated government minister to help eliminate corruption. Diella, the digital assistant meaning Sun, has been...
Read More
By infosecbulletin
/ Thursday , September 11 2025
On September 1, 2025, Qrator Lab identified and managed a major attack from the largest L7 DDoS botnet seen so...
Read More
By infosecbulletin
/ Thursday , September 11 2025
A new vulnerability, CVE-2025-4235, in Palo Alto Networks’ User-ID Credential Agent for Windows, could reveal a service account's password in...
Read More
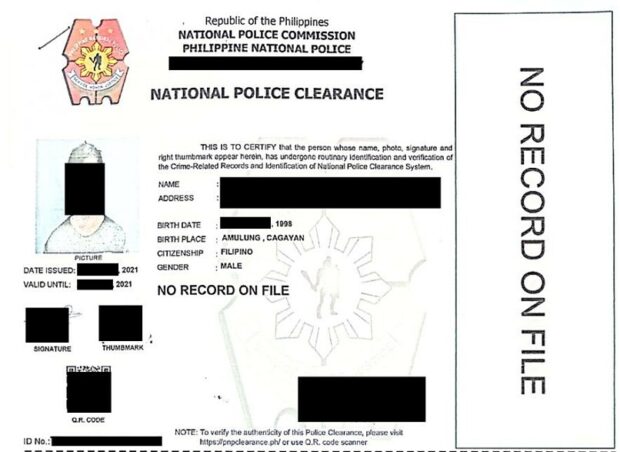
Sample of a criminologist accreditation, police clearance form, and BIR identification card, all available on the exposed database.
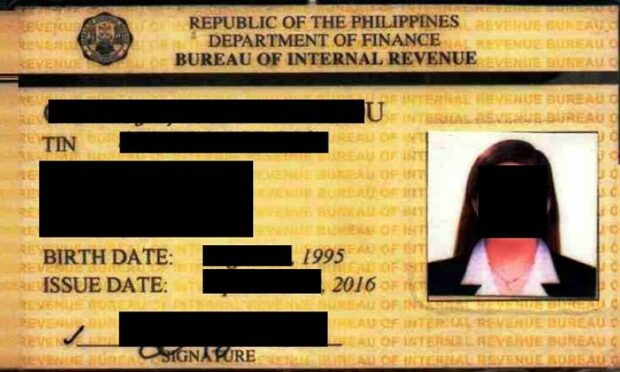
Sample of a criminologist accreditation, police clearance form, and BIR identification card, all available on the exposed database.
Internal directives addressing law enforcement officers were also exposed in the data breach.
“As an example, these would be orders from the top leadership of how to enforce what laws and what gets priority or additional training that is needed etc… I cannot further confirm or verify the accuracy or authenticity of these documents contained within this database. As such, I cannot guarantee that the contents of the documents are accurate or reliable,” writes cybersecurity researcher Jeremiah Fowler, who authored the report.
Fowler reported that these government documents were stored in an unsecured, non-password-protected database “readily accessible to individuals with an internet connection” and vulnerable to cyberattacks or ransomware. Fowler noted that law enforcement officers are at risk when their personal documents are exposed, but no such attacks have occurred.
“Any data breach that exposes personal information belonging to police and members of law enforcement or other officials can be dangerous. Individuals whose data is exposed could be potential victims of identity theft, phishing attacks, and a range of other malicious activities,” stressed Fowler.
“The availability of government records in an unsecured database raises concerns about potential national security issues. The exposed records could also potentially allow criminals to target members of law enforcement for blackmail or other schemes,” he added.
This database was left exposed for a minimum of six weeks, according to the report. However, Fowler recommended that a full forensic audit be conducted to “fully understand the extent and impact of the breach.”
PNP Public Information Office Chief Rederico Maranan relayed to INQUIRER.net a message from Anti-Cybercrime Group Director Police Brig. Gen. Sidney Hernia, stating that the cybercrime unit is still conducting vulnerability assessment and penetration testing.
“We cannot categorically say at this time that there was leaked applicants’ data… We also requested complete access logs from the PNP Recruitment and Selection Service (PRSS) to evaluate those logs,” he stated
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind