Global Secure Layer (GSL) recently mitigated a huge volume of DDoS attack ever recorded. The attack targeted a Minecraft gaming customer which peak at a staggering 3.15 billion packets per second (Gpps) that surpasses previous records by a factor of 3.2 to 3.5, underscoring the escalating threat posed by DDoS attacks.
On August 24th, The attack began targeting a single prefix of the victim’s network. This initial wave, peaking at 1.7 Gpps, lasted only 20 seconds which allowing the attackers to probe the network for weaknesses before launching a full-scale assault.
The attackers returned with a vengeance later on unleashing a massive back-to-back campaign that carpet-bombed all advertised prefixes of the victim’s network.
The peak of this attack reached an astonishing 3.15 Gpps, overwhelming private network interfaces (PNIs) between Korea Telecom and major tier 1 providers. Although the attack temporarily impacted some prefixes, particularly in New York, GSL’s swift reconfiguration of security settings prevented any long-term damage.
GSL’s said, the attackers used two distinct botnets during the assault. The first one is responsible for the record-breaking packet rate attack. This botnet’s composition was dominated by devices vulnerable to CVE-2023-2231, an authentication manipulation exploit. GSL identified over 42,000 sources participating in this attack, with a significant number traced back to Korea Telecom’s network.
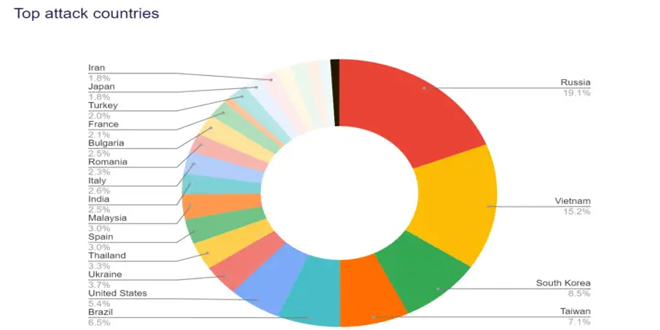
The second one focused on volumetric attacks, peaking at 1.516 terabits per second (Tbps). This botnet’s origins were more geographically diverse, with Russia, Ukraine, and Brazil leading the charge. The devices involved in these attacks included DrayTek Vigor routers and Hikvision IP cameras, showcasing the attackers’ ability to leverage widely available commercial hardware for their campaign.
GSL’s Goliath platform, deployed across 33 global points of presence, played a crucial role in mitigating the attacks. Goliath’s robust infrastructure and Creatia’s intelligent security configurations ensured that the impact on the customer was minimal. The attackers’ repeated attempts to breach the network were thwarted, with mitigation times consistently under 100 milliseconds.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind