Microsoft has the authority to decide how much money people will receive as a reward for finding and reporting vulnerabilities. The amount will depend on how serious the vulnerability is, how much damage it can cause, and the quality of the report.
ALSO READ:
By 2025, Domestic cloud market expected $46.3 million; MD “DataHub Asia”
The highest reward is available for high-quality reports of critical severity remote code execution vulnerabilities.
The Microsoft Defender Bounty Program currently focuses only on Microsoft Defender for Endpoint APIs. However, it is expected to expand to include other Defender products in the future.
“The Microsoft Defender Bounty Program invites researchers across the globe to identify vulnerabilities in Defender products and services and share them with our team,” said MSRC Senior Program Manager Madeline Eckert.
“Microsoft’s Bug Bounty programs represent one of the many ways we invest in partnerships with the global security research community to help secure Microsoft customers.”
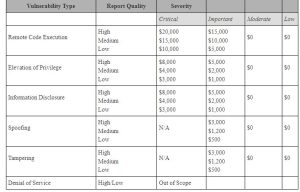
The complete list of in-scope security vulnerabilities includes:
Cross-site scripting (XSS)
Cross-site request forgery (CSRF)
Server-side request forgery (SSRF)
Cross-tenant data tampering or access
Insecure direct object references
Insecure deserialization
Injection vulnerabilities
Server-side code execution
Significant security misconfiguration (when not caused by the user)
Only component exploits are eligible for rewards. Merely finding an outdated library does not qualify.
If several security researchers submit bug reports for the same issue, Microsoft’s guidelines state that the initial submission will receive the bounty reward.
If a submission is eligible for more than one bounty program, the researchers will receive the largest reward from a single program. Further details regarding the Microsoft Bounty Program are available on this FAQ page.
Microsoft announced today that it paid a total of $58.9 million to 1,147 security researchers from around the world. These researchers reported 446 eligible vulnerabilities across 22 bug bounty programs.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind