Last year saw a significant rise in cyber threats, with malware becoming more advanced and attack strategies more sophisticated. A report by ANY.RUN, an interactive malware analysis platform, noted that 2024 experienced the highest levels of complex malware threats in the global cybersecurity landscape.
Surge in Malware Activity:
In 2024, ANY.RUN processed 4,001,036 public sandbox sessions, up 33% from 2,991,551 in 2023. Among these, 790,549 were confirmed malicious, and 211,517 were deemed suspicious, an increase from 148,124 suspicious sessions the previous year.
The analysis revealed 1.87 billion Indicators of Compromise (IOCs), almost three times the 640 million identified in 2023. This increase highlights the rise of advanced malware detection tools and more sophisticated cybercriminal tactics.
Top Malware Types of 2024:
Stealers became the most common threat in 2024, with 51,291 detections, up from 18,290 the year before.
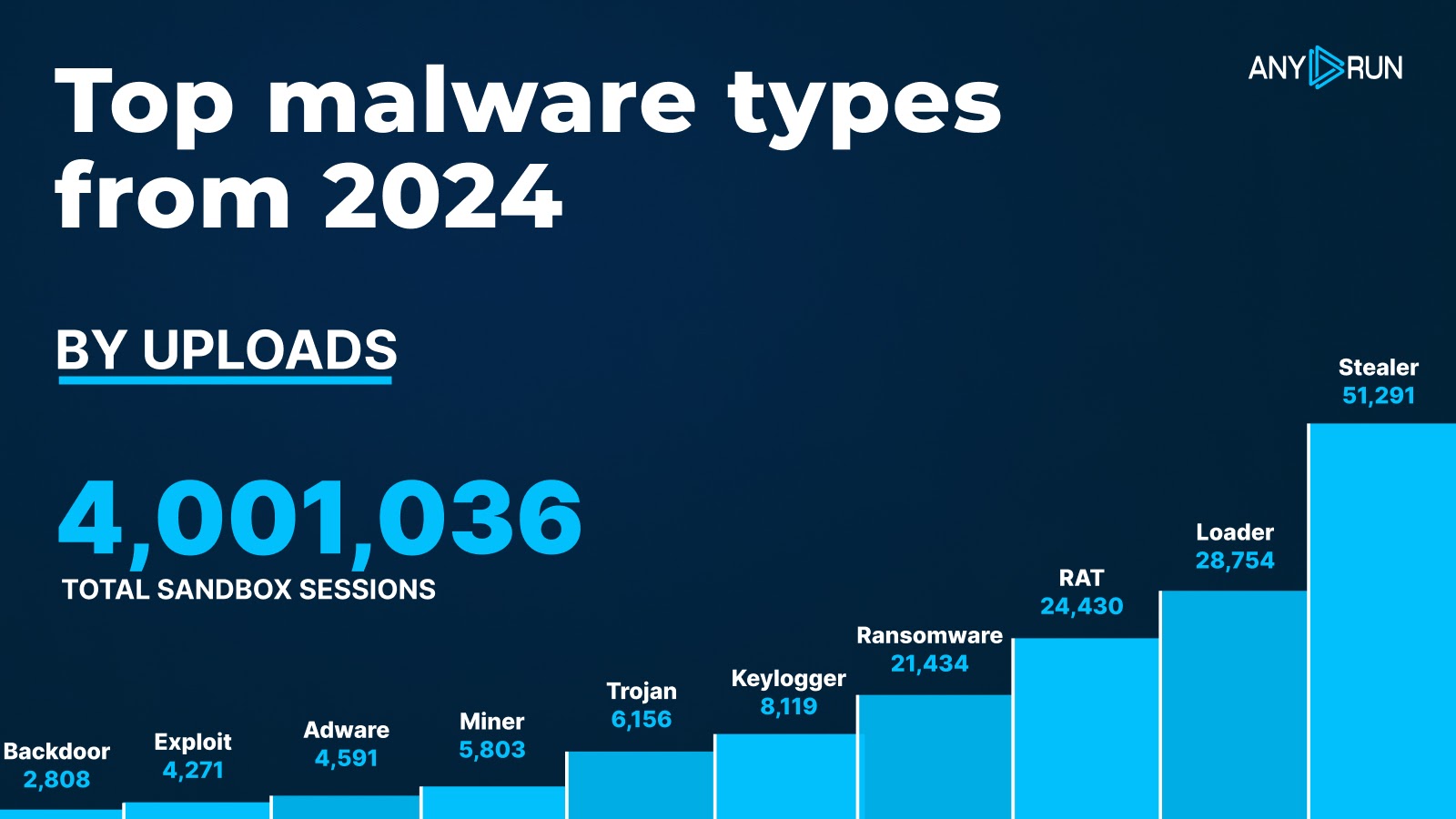
This indicates a significant rise in attackers prioritizing data theft. Other notable malware types included:
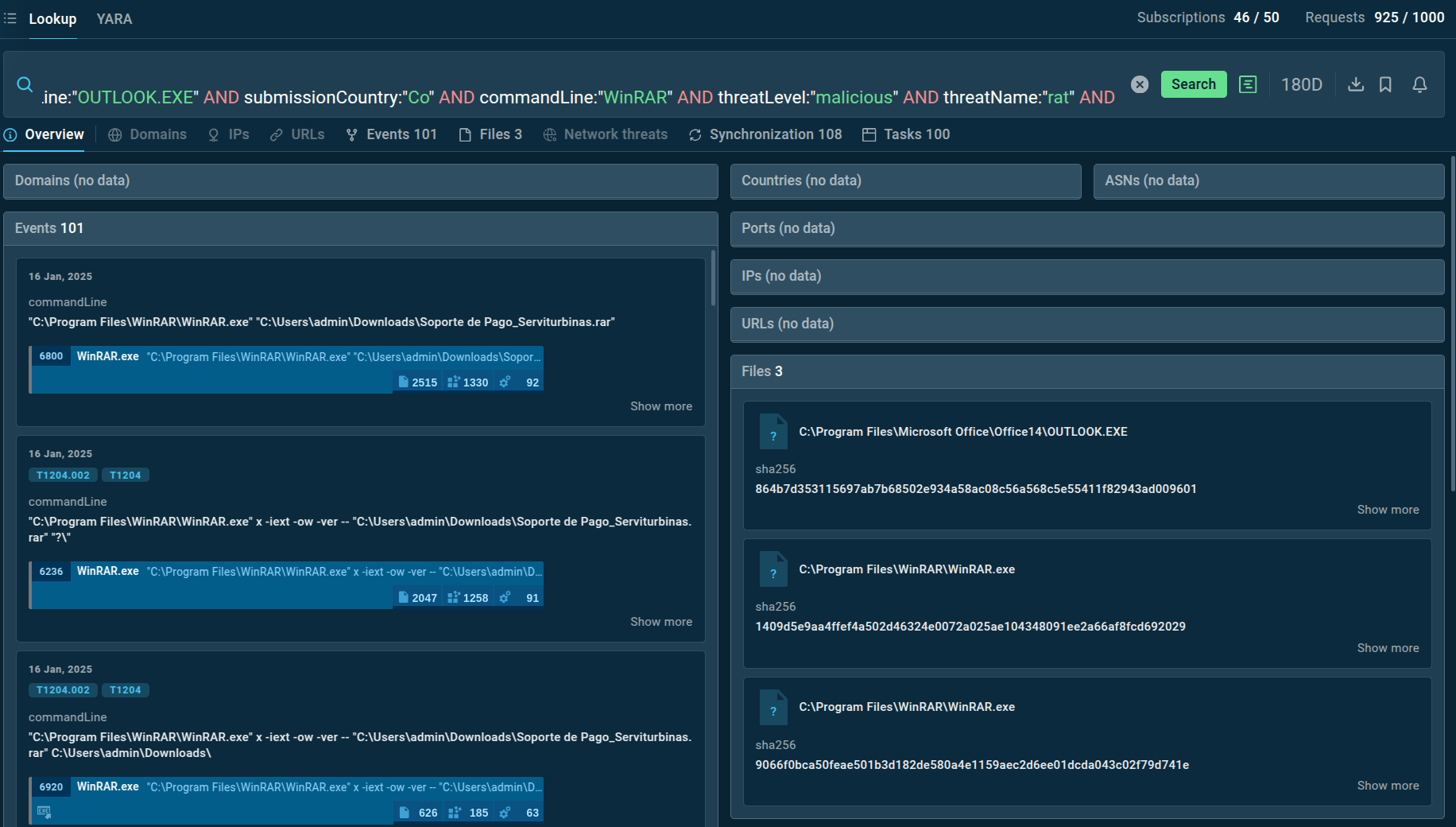
TI Lookup is a valuable tool for obtaining current threat intelligence. It allows you to search ANY.RUN’s extensive database for insights into emerging cyber threats, helping you stay ahead of potential risks.
Most Prevalent Malware Families:
In 2024, the malware rankings changed significantly. The newly recognized Lumma Stealer reached the top with 12,655 detections, indicating its quick adoption by cybercriminals.
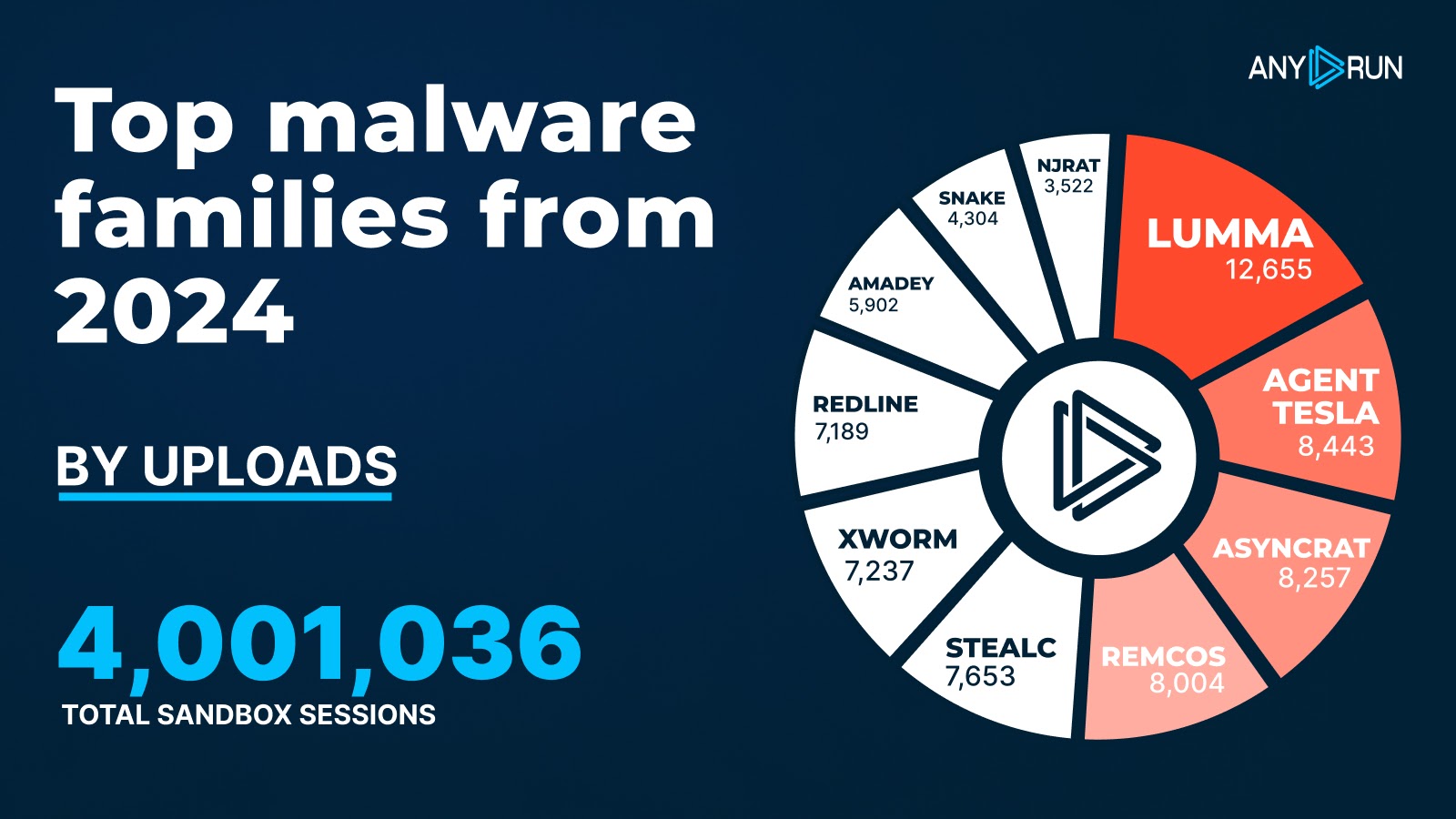
In 2023, popular names like Redline faced a decline, while new competitors like Stealc and Xworm indicate the evolving threat landscape.
In 2024, cyber threats increased in both number and complexity, with a notable rise in Stealers and new malware like Lumma Stealer. Attackers are innovating rapidly, especially using tools like PowerShell.
As we head into 2025, organizations need to invest in layered defenses, advanced threat detection, and continuous monitoring to tackle the changing cybersecurity challenges. Click here to read more.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














