Researchers found an attack targeting poorly secured Linux SSH servers using Supershell, a backdoor written in Go that gives attackers remote control of affected systems.
After the initial infection, attackers likely used scanners to find more vulnerable targets and launched dictionary attacks with credentials collected from the compromised systems.
The data shows a list of IP addresses used by threat actors along with root credentials, including common passwords such as “root/password” and “root/123456789.” Attackers often use these to access vulnerable systems.
The attacker used different methods to download and run harmful scripts after breaching a system. An attacker used wget, curl, tftp, and ftpget to download scripts from various sources, such as web servers and FTP servers, including non-standard ports.
The attacker ran downloaded scripts using shell commands, gaining remote access and possibly installing more malware. They also tried to cover their tracks by deleting the scripts and other related files.
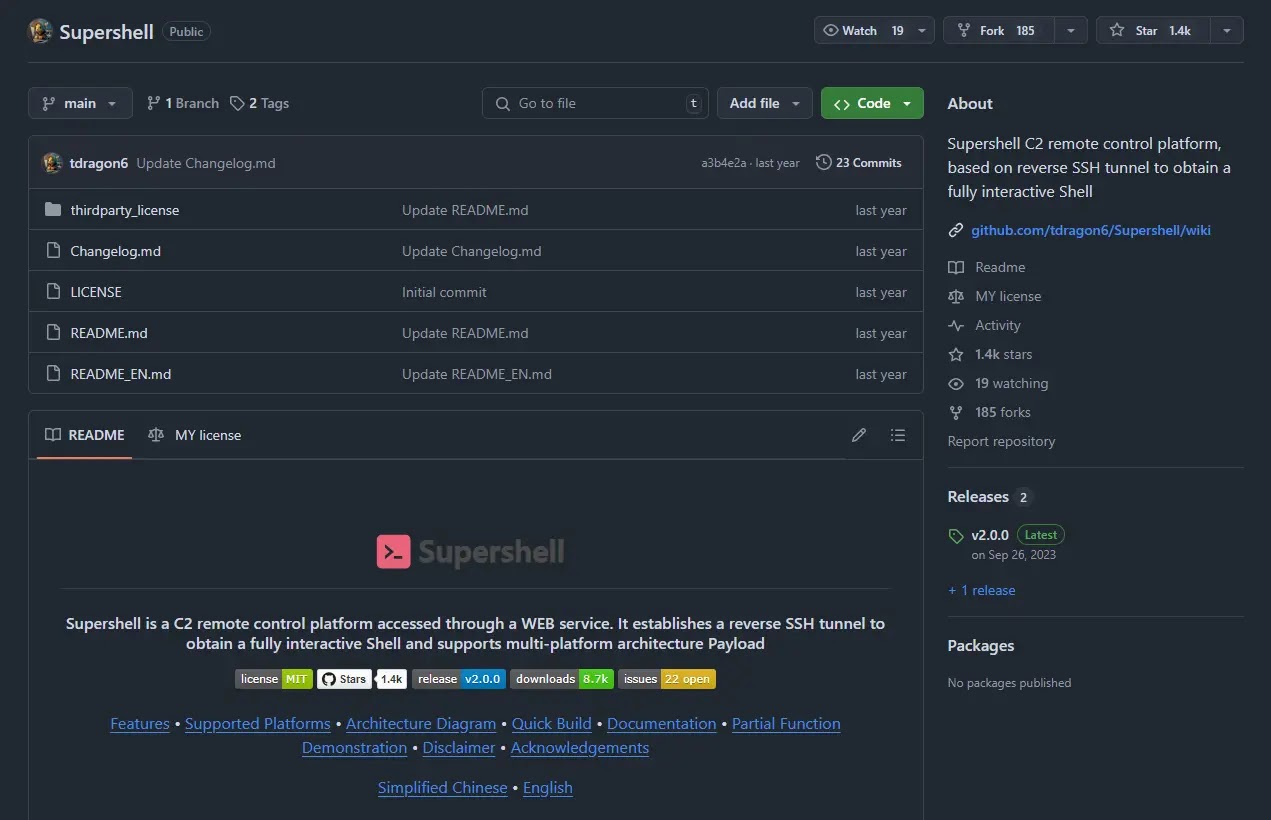
An attacker installed the disguised Supershell backdoor on a poorly managed Linux system, allowing them remote control, as indicated by its internal strings, behavior, and logs.
The main goal appears to be taking control of the system, but the attacker might also want to install a cryptocurrency miner, like XMRig, to exploit system resources for personal gain. This fits typical attack patterns targeting weak Linux systems.
Threat actors are taking advantage of insecure Linux SSH servers by installing the Supershell backdoor, allowing remote control of affected systems and leading to data theft and other malicious actions.
ASEC recommends that administrators focus on strong password practices, regular updates, and effective security measures like firewalls to mitigate this threat.
Keeping V3 updated is essential to prevent malware infections. These countermeasures can greatly reduce the risk of Supershell attacks for organizations.
The detected malware includes a Cobalt Strike backdoor, a shell agent downloader, and an ElfMiner downloader, identified as Backdoor/Linux.CobaltStrike.3753120, likely used for remote access and control.
The Downloader/Shell.Agent.SC203780 is a malicious shell agent that downloads and runs other harmful software. The ElfMiner downloader, Downloader/Shell.ElfMiner.S1705, was likely used to install cryptocurrency mining malware.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














