DataDog security researchers found that hackers are widely exploiting Docker Swarm, Kubernetes, and SSH servers. The newly discovered malware campaign focuses on “Docker” and “Kubernetes” environments and uses “Docker API” endpoint vulnerabilities as the ‘initial access vector.’
Hackers Exploiting Servers in Large Scale:
The hackers install “cryptocurrency mining software” on the compromised containers and use them to launch follow-up attacks.
These malicious payloads target the Kubernetes kubelet API, allowing attackers to allocate more resources and deploy additional malware. The campaign also uses a Docker hub to share the malware.
Under the name “nmlmweb3,” there are usernames of repositories that are malicious.
The attackers begin by using exposed Docker APIs to create an “Alpine container” and run an “init.sh” initialization script.
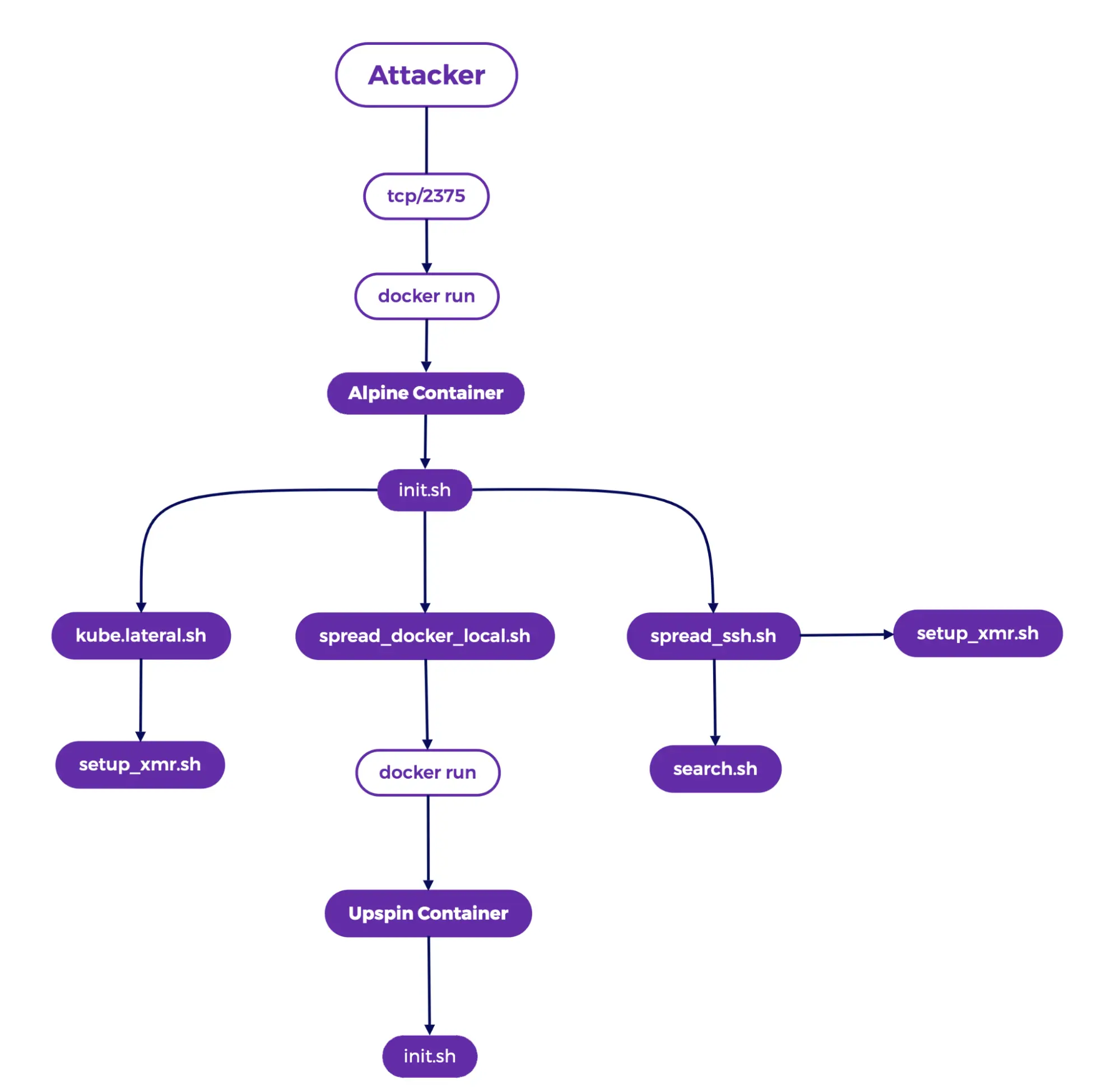
This script installs the “XMRig miner,” applies “process hiding techniques,” and “fetches additional payloads.”
Lateral movement is enabled via scripts against “Kubernetes” ‘kube.lateral.sh,’ “Docker” ‘spread_docker_local.sh,’ and “SSH” ‘spread_ssh.sh.’
In addition to using tools like “masscan” and “zgrab,” the malware also scans the network for vulnerable endpoints.
The malware disables security features, adds mining programs, and tries to spread to other machines.
The campaign also targets the perpetrator’s use of cloud services, specifically “GitHub” and “Codespaces,” in search of credential files.
Throughout the attack, the malware not only employs numerous “evasion techniques” but also tries to implement various strategies to maintain “persistence mechanisms.”
In this event the threat actors employed a “multi-stage approach,” initially exploiting exposed “Docker API endpoints” to gain access.
They then deployed various malicious payloads like “init.sh,” “kube.lateral.sh,” and “setup_xmr.sh,” which facilitated the “lateral movement” and “resource hijacking.”
The main aim was to mine cryptocurrency using the XMRig miner for Monero. They used scripts like “ar.sh” and “pdflushs.sh” for persistence, modifying iptables rules, adjusting system settings, and installing SSH backdoors.
The campaign demonstrated sophisticated evasion techniques like using “libprocesshider” to hide malicious processes.
Infrastructure analysis revealed connections to solscan[. ]live, a domain used for command and control (C2) and payload delivery.
While some tactics have coincided with those attributed to the “TeamTNT,” a known threat group. But here the final attribution still remains “uncertain.”
This attack illustrates the need for strong security measures in protecting “Docker” and “Kubernetes” deployments.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind