Check Point Research warns of the active exploitation of a new vulnerability, CVE-2025-24054, which lets hackers leak NTLMv2-SSP hashes using specially crafted .library-ms files. Microsoft patched this vulnerability on March 11, 2025. It affects all supported Windows versions and has been weaponized less than two weeks after its disclosure.
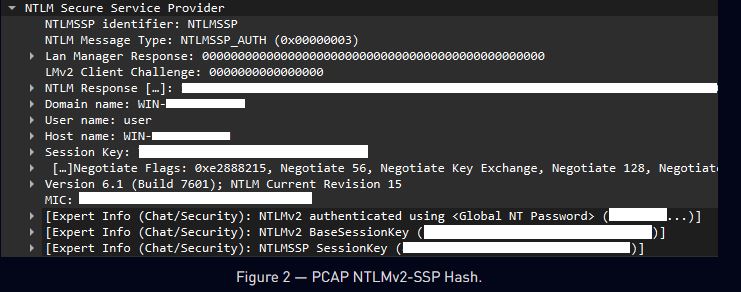
The flaw enables NTLM hash disclosure via spoofing and is triggered simply by interacting with a malicious .library-ms file. “This event will trigger Windows Explorer to initiate an SMB authentication request to a remote server and, as a result, it leaks the user’s NTLM hash without any user interaction,” the report states.
CVE-2025-24054 can be exploited through passive actions like right-clicking, dragging, or simply opening the folder with the malicious file, unlike traditional attacks that need users to open or execute files.
Despite Microsoft’s timely patch, attackers moved quickly. “Threat actors began actively exploiting CVE-2025-24054 just eight days after the patch was released,” Check Point confirmed.
The NTLM Exploits Bomb campaign was first detected around March 20–21, 2025, targeting government and private organizations in Poland and Romania. Victims received malicious Dropbox-hosted archives, which, when extracted, leaked NTLM hashes to attacker-controlled SMB servers in Russia, Bulgaria, the Netherlands, Australia, and Turkey.
Mitigations:
Microsoft’s prompt patching of CVE-2025-24054 was a crucial step; however, the rapid exploitation indicates that organizations must act swiftly to mitigate risks. Key recommendations include:
Apply patches: Update all affected systems with the latest security patches.
Strengthen network defenses: Use SMB signing, relay protections, and monitor SMB traffic for unusual activity.
Raise user awareness: Educate users on the dangers of untrusted archives and suspicious files.
Segment the network: Limit SMB traffic between segments to minimize risk.
Perform regular audits: Conduct vulnerability assessments and monitor for compromises.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














