A hacking group reportedly linked to Russian government has been discovered using a new phishing method that bypasses two-factor authentication by taking advantage of Google’s “app-specific password” feature.
Google’s Threat Intelligence Group reported that from April to early June, an operation pretended to be US State Department officials in emails, using perfect English and including four fake @state.gov colleagues.
Google has identified the threat actor as UNC6293, suspecting a connection to APT29, the Russian intelligence unit responsible for the 2016 Democratic National Committee breach. Investigators believe the group invested several weeks in meticulously planning each target before disseminating comprehensive guidance on the application-specific password (ASP) feature.
One victim, British writer Keir Giles of Chatham House, exchanged more than 10 emails with a sender calling herself “Claudie S. Weber.” The messages arrived during Washington business hours and used email addresses that never bounced.
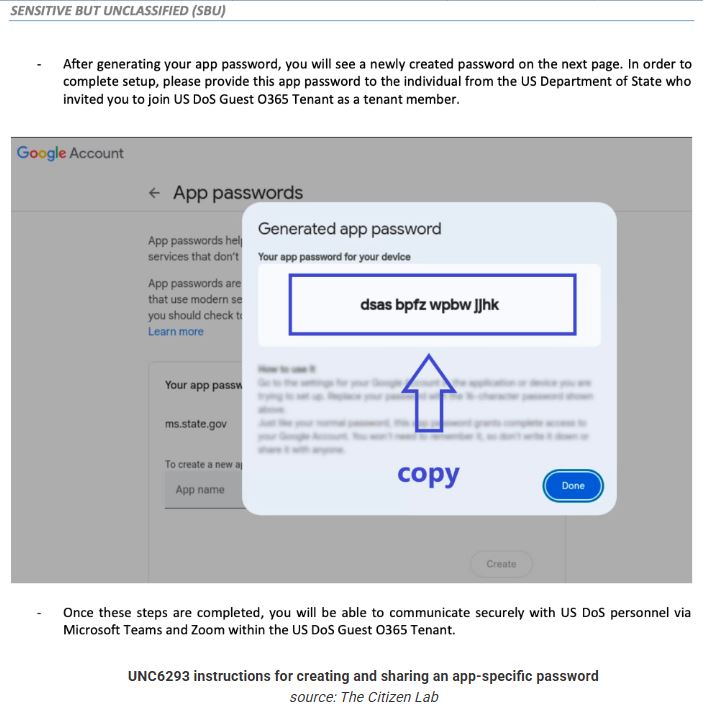
Once trust was established via email back-and-forth, Google said the impostor sent a six-page PDF on fake State Department letterhead instructing the target to visit Google’s account-settings page, generate a 16-character app-specific password labelled “ms.state.gov,” and email the code back “to complete secure onboarding.”
With that code, the hackers gained persistent, MFA-free access to the target’s Gmail account.
Citizen Lab examined the lure at Giles’s request and found the emails and PDF lacked common errors in phishing attempts. They believe generative AI was used to improve the language and make it less suspicious.
“This was a highly sophisticated attack, requiring the preparation of a range of fake identities, accounts, materials and elements of deception. The attacker was clearly meticulous, to the extent that even a vigilant user would be unlikely to spot out-of-place elements or details,” Citizen Lab researchers said.
Google linked the Giles incident to a second wave centered around Ukrainian themes. In both cases, the attackers routed logins through the same residential-proxy IP and occasionally reused the node across different victims.
The tech giant stated it has disabled all stolen passwords, secured affected accounts, and notified more users.
Google and Citizen Lab urge high-profile targets to enrol in Google’s Advanced Protection feature and audit accounts for any lingering ASPs.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind













