Advertisement for selling the credentials of allegedly belonging to Indian government emails surfaced on the dark web marketplace. A hacker on a private forum claims that purchasing access to these government email accounts can make anyone willing to pay a few thousand rupees “become” a government officer.
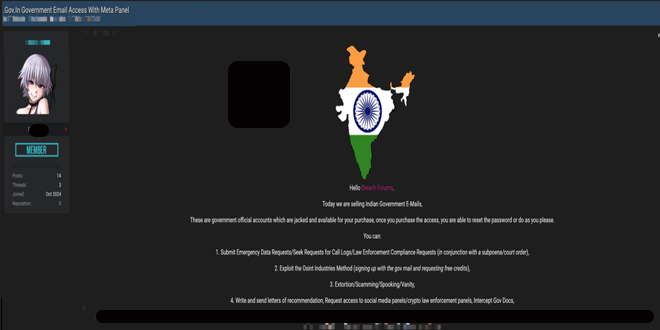
The forum post reads, “Once you purchase the access, you will be able to reset the password or do as you please,” reads a post on the hacking forum.
But how exactly could these government emails be misused? India today reported, Take, for example, “digital arrest.” With basic information like a person’s name, phone number, and address–often readily available in public records—cybercriminals posing as law enforcement can “arrest” their victims and extort large sums of money. This tactic, known as “digital arrest,” has become a lucrative form of online fraud.
Consider the potential actions a cybercriminal could take if they had access to a target’s purchase history, payment recipients, online searches, visited websites, and social media chats.
Sale of .gov.in email accounts:
India Today’s OSINT team discovered three ads on a hacking forum, with the latest posted on November 6, promoting the sale of email IDs and their passwords.
The team examined nine email accounts from Tamil Nadu government officials with the @tn.gov.in domain. These accounts were included in a batch of 700 credentials offered by a seller, and one account seemed to belong to an IAS officer.
Although government email accounts require two-factor authentication, the Indian government mandated the use of the Kavach app in 2020 for added security. This app requires users to approve sign-in attempts from new devices. However, hackers seem to have found a way to bypass this security.
A cybercriminal told India Today they sell government email credentials for $150 (around Rs 12,600). They offered to demonstrate their access by logging into one account. The transaction uses an escrow service where forum admins hold the buyer’s payment until the seller successfully logs in.
Other sellers are offering “logs” that contain data which can be further exploited to extract email usernames and passwords. “Today I’ll be selling Indian Government Logs. The file contains over 40,000 lines full of logs,” read a forum post by a cybercriminal in September this year.
In its November 4 advisory, the FBI warned that hacked .gov.in email accounts could be misused to request emergency data from companies under false pretenses, claiming it’s needed for urgent investigations.
The FBI advisory and hacker posts show that hacked government emails could be used to ask telecom companies for call logs, carry out scams, and commit crimes such as digital arrests. They could also be used to get information from social media and cryptocurrency exchanges about their users. For instance, Meta’s “Law Enforcement Online Requests” center allows verified government emails to request user data.
Source: India today, Darkweb
(Media Disclaimer: This report is based on research conducted internally and externally using different ways. The information provided is for reference only, and users are responsible for relying on it. Infosecbulletin is not liable for the accuracy or consequences of using this information by any means)
Cyberattacks increase 105% in third quarter of 2024 in Bangladesh
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














