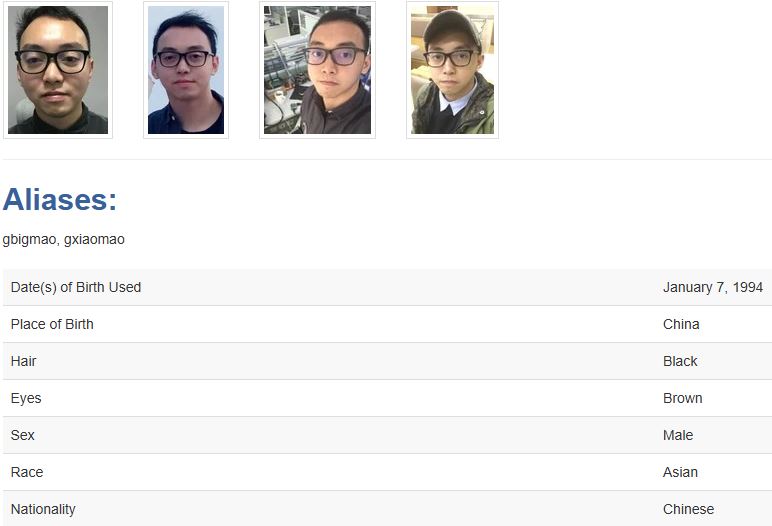
A federal court in Hammond, Indiana, has unsealed an indictment against Guan Tianfeng, a Chinese citizen, for allegedly hacking firewall devices globally in 2020. Guan and his co-conspirators, employed by Sichuan Silence Information Technology Co. Ltd., targeted a previously unknown vulnerability (an “0-day” vulnerability) in firewalls produced by U.K.-based Sophos Ltd., a cybersecurity firm.
The malware created by Guan was meant to steal information and encrypt files on infected computers if victims tried to fix the issue. Overall, Guan and his team infected around 81,000 firewall devices globally, including one used by a U.S. agency.
“The defendant and his co-conspirators exploited a vulnerability in tens of thousands of network security devices, infecting them with malware designed to steal information from victims around the world,” said Deputy Attorney General Lisa Monaco. “Today’s indictment reflects the Justice Department’s commitment to working with partners across government and across the globe to detect and hold accountable malicious cyber actors based in China or elsewhere who pose a threat to global cybersecurity.”
Assistant Attorney General Matthew G. Olsen stated, “The defendant and his associates compromised tens of thousands of firewalls, putting devices that protect computers worldwide at risk. The Department of Justice will hold accountable those involved with China-based companies that carry out indiscriminate hacks and harm global cybersecurity.”
The US Department of State has offered a reward of up to $10 million for information about Sichuan Silence or Guan. Due to sanctions, any money or assets they hold in the US must be blocked and reported to OFAC.
The Treasury’s OFAC reported that Tianfeng used a zero-day exploit to install malware on about 81,000 firewalls belonging to various businesses worldwide from April 22 to 25, 2020.
Over 23,000 of these firewalls were in the US, including 36 that safeguarded critical infrastructure companies.
The SQLi vulnerability (CVE 2020-12271) was exploited with a command injection to gain root access and install the Asnarök Trojan on the device.
Sophos’ rapid response mitigated potential damage, but the attack continues to highlight that “the scale and persistence of Chinese nation-state adversaries poses a significant threat to critical infrastructure, as well as unsuspecting, everyday businesses,” Sophos said.
In October 2024, cybersecurity company Sophos began a five-year study tracking coordinated campaigns by Chinese groups targeting perimeter devices from 2018-2023, called ‘Pacific Rim.’
Ross McKerchar, CISO at Sophos, supported the sanctions, highlighting the importance of working together to address the threat from Chinese groups.
“The scale and persistence of Chinese nation-state adversaries poses a significant threat to critical infrastructure, as well as unsuspecting, everyday businesses as noted in Sophos’ Pacific Rim investigation report. Their relentless determination redefines what it means to be an Advanced Persistent Threat; disrupting this shift demands individual and collective action across the industry, including with law enforcement,” he noted.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind