A large dataset belonging to BSNL, an Indian state-owned telecommunications company, has been put up for sale by cybercriminals on an underground forum.
On May 27, 2024, it was discovered that “kiberphant0m” was selling unauthorized access to databases stolen from BSNL, as well as data from other Asian telecom companies reports thecyberexpress.
According to the threat actor known as kiberphant0m, the leaked data contains sensitive information like IMSI, SIM details, HLR (Home Location Register), DP Card Data, Masterkeys, and more.
Details of the Allegedly Compromised Data:
The attacker claims to possess a comprehensive collection of BSNL data, including:
IMSI (International Mobile Subscriber Identity)
SIM details
HLR (Home Location Register) information
Machine Copy Data
DP Card Data (8GB)
DP Security Key Data (130GB)
Masterkeys
SOLARIS server snapshot (140GB)
Main database (3.5GB)
The leaked dataset supposedly has important information about BSNL’s operations and customer records. Some of the fields in the main database structure are SIM, IMSI, PIN1, PUK1, PIN2, PUK2, ADM, AUTH, KDBID, ALGOID, ACSUB, AMF, and MAKE dailydarkweb reports reads.
The alleged breach involves a person who is selling the data on Telegram for a negotiable price ranging from $80,000 to $150,000. They have also mentioned that they are willing to sell this data to anyone, including state actors, if the Indian government does not take immediate action to acquire and protect the compromised information.
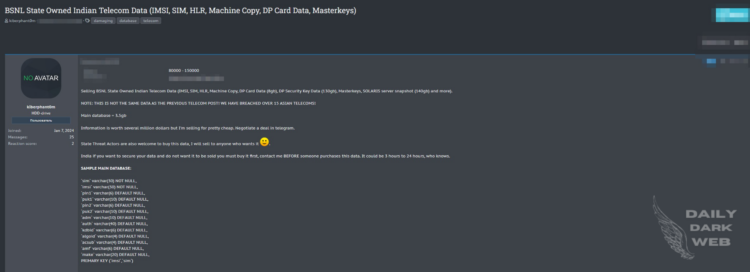
BSNL has yet to issue an official statement or response regarding the breach, leaving the claims unverified. The threat actor said to an international media that, “This is not the same data as the previous telecom post! we have breached over 15 Asian telecoms! Information is worth several million dollars but I’m selling for pretty cheap. Negotiate a deal on telegram. State Threat Actors are also welcome to buy this data, I will sell to anyone who wants it.”
Additionally, CloudSEK’s XVigil platform reported in middle of May that a threat actor named “303” who posted an ad on BreachForums offering access to a shell account on a Telecom Argentina server. This type of access gives the user a lot of control over the server, which could be used for stealing data, installing malware, or causing disruptions.
The ad also said the hacker has 121GB of data on the server. Although the type of data is not specified, the large amount suggests it could include important customer info, financial records, or internal company documents.
(Media Disclaimer: This report is based on research conducted internally and externally using different ways. The information provided is for reference only, and users are responsible for relying on it. Infosecbulletin is not liable for the accuracy or consequences of using this information by any means)
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














