A major security flaw in Craft CMS, a popular PHP content management system, has been found, enabling unauthenticated remote code execution (RCE) with default settings.
The vulnerability CVE-2024-56145 was reported by security researchers and quickly patched by the Craft CMS team within 24 hours.
PHP has improved over the years but still faces security challenges. While older vulnerabilities like register_globals and magic_quotes_gpc are resolved, some design quirks can cause critical issues.
The recent flaw in Craft CMS shows how ordinary PHP behaviors can lead to security vulnerabilities.
At the heart of this vulnerability is the register_argc_argv configuration setting in PHP. This setting controls if command-line arguments ($_SERVER[‘argc’] and $_SERVER[‘argv’]) are available when a script runs.
In PHP, the register_argc_argv option is enabled by default, which can cause issues when query strings are used in web-hosted scripts. The official Craft CMS Docker image has this setting enabled, making it potentially vulnerable.
How the Vulnerability Works:
The issue with Craft CMS is in its handling of command-line options during startup. Developers found that query strings can manipulate paths for important files, such as configuration files and templates.
Attackers could exploit this behavior to control file paths and execute arbitrary code.
Researchers showed that using an ftp:// link to host malicious templates on an FTP server allowed them to bypass security checks and inject harmful code into a vulnerable Craft CMS.
Adam Kues found that Craft CMS’s attempt to secure its template engine (Twig) wasn’t foolproof. Attackers could use tricks like the sort filter combined with call_user_func to bypass these security measures and execute remote code.
Impact and Mitigation:
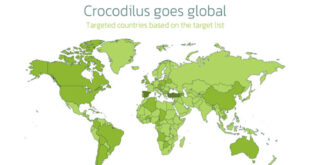
Craft CMS is used by over 150,000 websites worldwide, including major enterprises. A vulnerability risked organizations using the platform’s default settings.
The Craft CMS team quickly released patched versions 5.5.2+ and 4.13.2+. Users should upgrade their installations right away. Full report here.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind