Utilizing Fortinet’s FortiClient EMS a news campaign has emerged. According to Vedere labs of forescout’s report this campaign leverages a critical vulnerability identified as CVE-2023-48788 and The campaign has been active since at least 2022 as stated the report.
CVE-2023-48788:
According to the official documentation, FortiClient Enterprise Management Server (EMS) is a “security management solution that enables scalable and centralized management of multiple endpoints.”
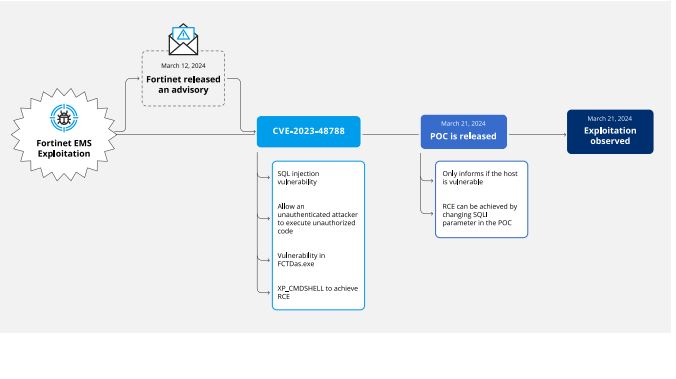
On March 12, Fortinet published an advisory about CVE-2023-48788, a SQL injection vulnerability in the Data Access Server (DAS) component of EMS which translates requests received by the FcmDaemon, the main application of EMS listening on port 8013, into SQL and interacts with the Microsoft SQL Server database which is part of the EMS installation.
The advisory states that unauthenticated attackers can achieve Remote Code Execution (RCE) via an SQL injection and scores the CVE as critical (CVSS score 9.8). The advisory also mentioned that this vulnerability was exploited in the wild and that Fortinet released a virtual patch named FG-VD54509 0day :FortiClientEMS.DAS.SQL. Injection ” to fix the issue.
On March 21, researchers released a proof of concept (PoC) exploit for CVE-2023-48788 and detailed that its root cause was missing sanitization of the FCTUID parameter. The vulnerability can be exploited by appending an SQL statement – such as the traditional “’ OR 1=1 –” test – to FCTUID in a request to FcmDaemon. Different effects can be obtained by changing the appended SQL statement. Full RCE can be achieved, for example, by enabling the xp_cmdshell stored procedure on the SQL server that EMS uses which spawns a Windows command shell and executes a string passed by the attacked.
The Connect:fun campaign is particularly notable for its use of ScreenConnect and Powerfun as post-exploitation tools, marking it as Vedere Labs’ first-ever named campaign.
The incident that brought this campaign to light involved a media company whose FortiClient EMS was vulnerable and exposed to the internet.
The attack was not an isolated event. Scanning activity from the IP address 185[.]56[.]83[.]82 was observed targeting FortiClient EMS across various customer networks.
This activity began on March 21 and persisted through several days, indicating a concerted effort by the attackers to exploit the vulnerability across multiple potential victims.
The exploitation of CVE-2023-48788 poses a significant threat to organizations, as it can lead to unauthorized access and control over the FortiClient EMS.
This control can result in further malicious activities, including data theft, lateral movement within the network, and potentially a full-scale breach of the organization’s cyber defenses.
Mitigation recommendations, TTPs and IoCs:
To mitigate against exploitation of CVE-2023-48788, follow these steps:
• Apply the patch provided by Fortinet.
• Ensure that the traffic reaching FortiClient EMS is constantly monitored for signs of exploitation by using
an intrusion detection systems (IDS).
• Consider using a web application firewall (WAF) to block potentially malicious requests.
• Use the IoCs and TTPs shared below for threat detection and hunting in your network.
Source: Forescout, gbhackers
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














