Cisco released its semiannual Cisco IOS and IOS XE Software Security Advisory Bundled Publication on March 27, 2024. In direct response to customer feedback, Cisco releases bundles of Cisco IOS and IOS XE Software Security Advisories on the fourth Wednesday of the month in March and September of each calendar year.
The March 27, 2024, release of the Cisco IOS and IOS XE Software Security Advisory Bundled Publication includes 13 Cisco Security Advisories that describe 14 vulnerabilities in Cisco IOS Software and Cisco IOS XE Software. Cisco has released software updates that address these vulnerabilities.
Details:
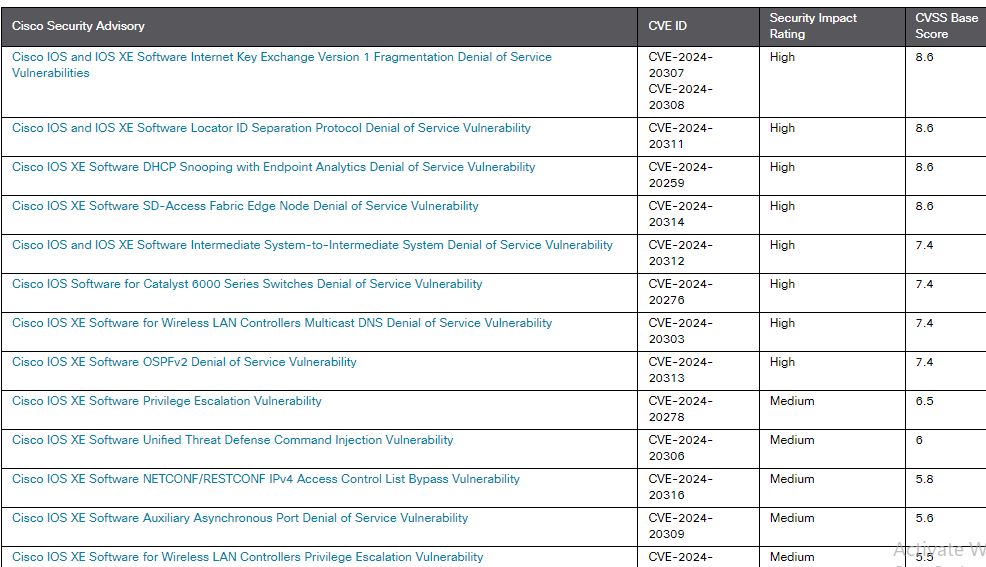
The following table identifies Cisco Security content that is associated with this bundled publication:
Cisco Access Point Software Secure Boot Bypass Vulnerability:
A vulnerability in the boot process of Cisco Access Point (AP) Software could allow an unauthenticated, physical attacker to bypass the Cisco Secure Boot functionality and load a software image that has been tampered with on an affected device.
This vulnerability exists because unnecessary commands are available during boot time at the physical console. An attacker could exploit this vulnerability by interrupting the boot process and executing specific commands to bypass the Cisco Secure Boot validation checks and load an image that has been tampered with. This image would have been previously downloaded onto the targeted device. A successful exploit could allow the attacker to load the image once. The Cisco Secure Boot functionality is not permanently compromised.
Cisco has released software updates that address this vulnerability. There are no workarounds that address this vulnerability.
This advisory is available at the following link:
https://sec.cloudapps.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-ap-secureboot-bypass-zT5vJkSD
Cisco Access Point Software Denial of Service Vulnerability:
A vulnerability in the IP packet processing of Cisco Access Point (AP) Software could allow an unauthenticated, remote attacker to cause a denial of service (DoS) condition on an affected device.
This vulnerability is due to insufficient input validation of certain IPv4 packets. An attacker could exploit this vulnerability by sending a crafted IPv4 packet either to or through an affected device. A successful exploit could allow the attacker to cause an affected device to reload unexpectedly, resulting in a DoS condition. To successfully exploit this vulnerability, the attacker does not need to be associated with the affected AP. This vulnerability cannot be exploited by sending IPv6 packets.
Cisco has released software updates that address this vulnerability. There are no workarounds that address this vulnerability.
This advisory is available at the following link:
https://sec.cloudapps.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-ap-dos-h9TGGX6W
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














