On Wednesday, CISA alerted about increased breach risks due to the earlier compromise of legacy Oracle Cloud servers, emphasizing the serious threat to enterprise networks.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) issued a warning about the risks of using embedded or reused credentials.. The agency noted that while the full scope of the breach remains unconfirmed, it poses “potential risk to organizations and individuals, particularly where credential material may be exposed, reused across separate, unaffiliated systems, or embedded (i.e., hardcoded into scripts, applications, infrastructure templates, or automation tools).”
CISA cautioned that these credentials can be difficult to detect, allowing unauthorized access for a long time once they’re compromised.
“The compromise of credential material, including usernames, emails, passwords, authentication tokens, and encryption keys, can pose a significant risk to enterprise environments,” the agency stated.
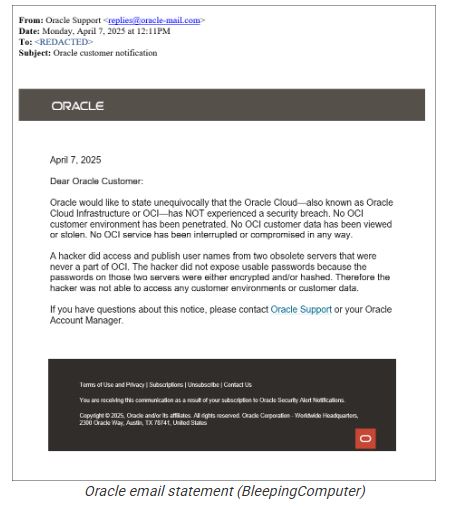
This warning comes after Oracle confirmed in email notifications sent to customers that a threat actor leaked credentials stolen from what the company described as “two obsolete servers.”
BleepingComputer reported” The hacker behind the breach posted newer records from 2025 on BreachForums and shared data with them from the end of 2024. They claimed “they separately confirmed with multiple Oracle customers that leaked data samples (including associated LDAP display names, email addresses, given names, and other identifying information) received from the threat actor were valid”.
CISA said, Threat actors routinely harvest and weaponize such credentials to:
Escalate privileges and move laterally across networks
Access cloud and identity management systems
Conduct phishing, credential stuffing, and BEC attacks
Sell or exchange access in criminal marketplaces
Enrich the data for resale or targeted intrusion campaigns
To combat potential fallout, CISA recommends immediate action:
For Organizations:
Reset affected passwords, especially where credentials aren’t managed through centralized identity systems
Audit scripts and templates for embedded credentials; replace them with secure, centralized secret management
Monitor login logs for suspicious activity involving privileged or federated identities
Enforce phishing-resistant MFA wherever feasible
For Individual Users:
Update any reused passwords and enable phishing-resistant MFA
Use unique, complex passwords across services
Remain vigilant for phishing attacks disguised as password resets or suspicious login alerts
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














