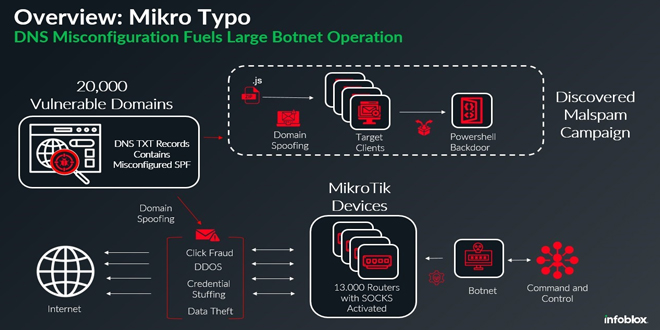
A recent Infoblox Threat Intel report reveals a sophisticated botnet that exploits DNS misconfigurations to spread malware widely. This botnet, made up of about 13,000 compromised MikroTik devices, uses fake sender domains and malicious emails to deliver trojan malware and engage in other harmful activities.
According to the report, “This botnet uses a global network of MikroTik routers to send malicious emails that are designed to appear to come from legitimate domains.” The attackers take advantage of DNS errors, especially in SPF records, which let emails from unauthorized servers look legitimate.
Infoblox found that about 20,000 sender domains were impacted, primarily due to misconfigured SPF records. These records, published as TXT entries in a domain’s DNS, can permit any server to send emails on behalf of the domain if set up incorrectly.
A correctly configured SPF record looks like this:
v=spf1 include:example.com -all
However, the botnet exploited domains with misconfigurations such as:
v=spf1 include:example.com +all
The inclusion of “+all” effectively permits any server to send emails on behalf of the domain, nullifying SPF protections.
The campaign’s emails imitated shipping companies like DHL, using subject lines about invoices or tracking. They included zip file attachments named “Invoice###.zip” or “Tracking###.zip.” Inside, Infoblox discovered obfuscated JavaScript files that ran PowerShell scripts, linking victims to a command-and-control server tied to suspicious Russian activity.
MikroTik routers are vulnerable due to firmware flaws, including a hardcoded ‘admin’ account with a blank password. This weakness has allowed attackers to use the routers as SOCKS proxies, turning them into anonymous relays for malicious traffic.
Infoblox states, “Enabling SOCKS effectively turns each device into a proxy, masking the true origin of malicious traffic and making it harder to trace back to the source.” The compromised routers facilitated various attacks, including:
Malware Delivery: Using proxies to bypass security filters.
Data Exfiltration: Sending sensitive data to attacker-controlled servers.
Phishing Campaigns: Amplifying the scale of malicious email campaigns.
The report concludes, “Each compromised device becomes a cog in a much larger, nefarious machine, capable of wreaking havoc on unsuspecting targets.”
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind