Bangladeshi Social media posts have raised concerns about unauthorized withdrawals from bank accounts, affecting at least 7 to 8 people who hold dual currency or credit cards. Initial findings suggested two banks are reported to impacted.
Bangladesh Cyber Security Intelligence (BCSI) reported unauthorized transactions made via Facebook Ad Manager, often in small amounts, with one account having 315 transactions. Victims did not receive One-Time Password (OTP) notifications for these transactions.
The unusual nature of these incidents has caught the attention of the BCSI, is now investigating how these breaches happened without standard security measures like OTP verification.
So what might have happened?
When adding a card for Facebook ad payments, minimal information like the card number, DOB, and CVC/CVV is required. The platform might sometimes ask for a postal code but never for the cardholder’s name. The ease of adding a card without extensive verification leads to vulnerabilities.
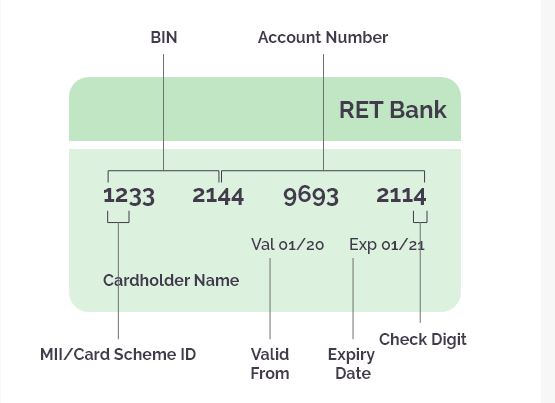
For example, if the card’s BIN (Bank Identification Number) is compromised, crackers can generate and use other card numbers sequentially linked to the original BIN. Additionally, transactions through verified international gateways might not prompt an OTP from the bank, assuming it’s a legitimate request, hence bypassing usual security checks. This process, facilitated by tools and unique IP usage by platforms like Facebook, can lead to unauthorized use of your card without detection.
What is a BIN Attack?
In a BIN attack, A cybercriminal uses brute force methods to find valid credit card details like the card number, expiration date, and CVV. They utilize a botnet to quickly test many combinations. Once they find a valid set, they may try variations, assuming other cards have the same Bank Identification Number (BIN).
Way to prevent Bin attacks to enhance securit:
BIN attacks occur when fraudsters use the Bank Identification Number to create valid card numbers, but can be reduced through several measures by banks and cardholders. Here BCSI suggest:
Measures to be taken for Banks:
Enhanced Verification: Incorporate advanced security protocols, including biometric authentication and mandatory CVV verification for every transaction.
Limit Number of Attempts: Set a limit on how many times a card number can fail verification before being blocked or flagged.
Advanced Fraud Detection Systems: Utilize AI and machine learning to identify unusual patterns of BIN attacks.
Secure BIN Sharing: Limit shared BIN data with merchants and manage it securely to prevent unauthorized access.
Monitor Transaction Patterns: Regularly monitor transaction patterns for anomalies that may signal a BIN attack, like an unusually high number of declined transactions.
Educate Merchants: Provide training and resources to merchants on identifying and responding to potential BIN attacks.
Measures to be taken for Card Users:
Monitor Account Activity: Check your transaction history often for any suspicious activity and report it right away.
Use Card Security Features: Turn on security options for your card, like temporary numbers for online shopping.
Enable Alerts: Configure transaction notifications through SMS or email to receive updates on any charges made with the card.
Be Cautious Online: Only enter card details on secure, familiar websites. Check for “HTTPS” in the URL as a sign of security.
Report Lost/Stolen Cards Immediately: Promptly notify the bank about any lost or stolen cards to safeguard against unauthorized transactions.
Source: BCSI
(Media Disclaimer: This report is based on research conducted internally and externally using different ways. The information provided is for reference only, and users are responsible for relying on it. Infosecbulletin is not liable for the accuracy or consequences of using this information by any means)
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














