Barracuda, fixed a zero-day bug on December 21. The bug was used by hackers known as UNC4841 to exploit Email Security Gateway (ESG) appliances.
The company released additional security updates the following day for compromised ESG appliances that were attacked with SeaSpy and Saltwater malware.
A security vulnerability was disclosed on Christmas Eve and is tracked as CVE-2023-7102. This zero-day is caused by a weakness in the Spreadsheet::ParseExcel third-party library, which is used by the Amavis virus scanner on Barracuda ESG appliances.
Attackers can exploit the flaw to execute arbitrary code on unpatched ESG appliances through parameter injection.
The company also filed the CVE-2023-7101 CVE ID to track the bug in the open-source library. A patch is still pending.
“No action is required by customers at this time, and our investigation is ongoing,” Barracuda said in an advisory issued on December 24.
“Barracuda, working in collaboration with Mandiant, assesses this activity is attributable to continued operations of the China nexus actor tracked as UNC4841.
“For organizations utilizing Spreadsheet::ParseExcel in their own products or services, we recommend reviewing CVE-2023-7101 and promptly taking necessary remediation measures.”
Attackers can exploit the flaw to take control of unpatched ESG appliances.
“We also reported the CVE-2023-7101 CVE ID for the bug in the open-source library, which is still awaiting a patch.”
“No action is required by customers at this time, and our investigation is ongoing,” Barracuda said in an advisory issued on December 24.
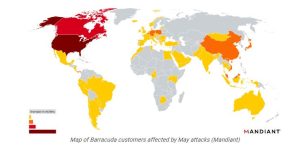
Barracuda, with the help of Mandiant, confirms that this activity is linked to the ongoing operations of the China-based group known as UNC4841.
“For organizations utilizing Spreadsheet::ParseExcel in their own products or services, we recommend reviewing CVE-2023-7101 and promptly taking necessary remediation measures.”
“The attackers’ motivation was espionage, with UNC4841 hackers engaging in targeted data theft from breached networks to high-profile government and high-tech users.”
Almost a third of appliances hacked in the May campaign belonged to government agencies, most of them between October and December 2022, according to cybersecurity firm Mandiant.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














