Cybernews has uncovered a huge data leak at MC2 Data, a background check company, impacting many US citizens. MC2 Data and similar companies provide public records and background check services by collecting and analyzing data from various public sources, such as criminal records, employment history, family information, and contact details.
They use this information to create comprehensive profiles that employers, landlords, and others rely on for decision-making and risk management.
Websites that MC2 Data operates include:
PrivateRecords.net
PrivateReports
PeopleSearcher
ThePeopleSearchers
PeopleSearchUSA
mc2 data leak
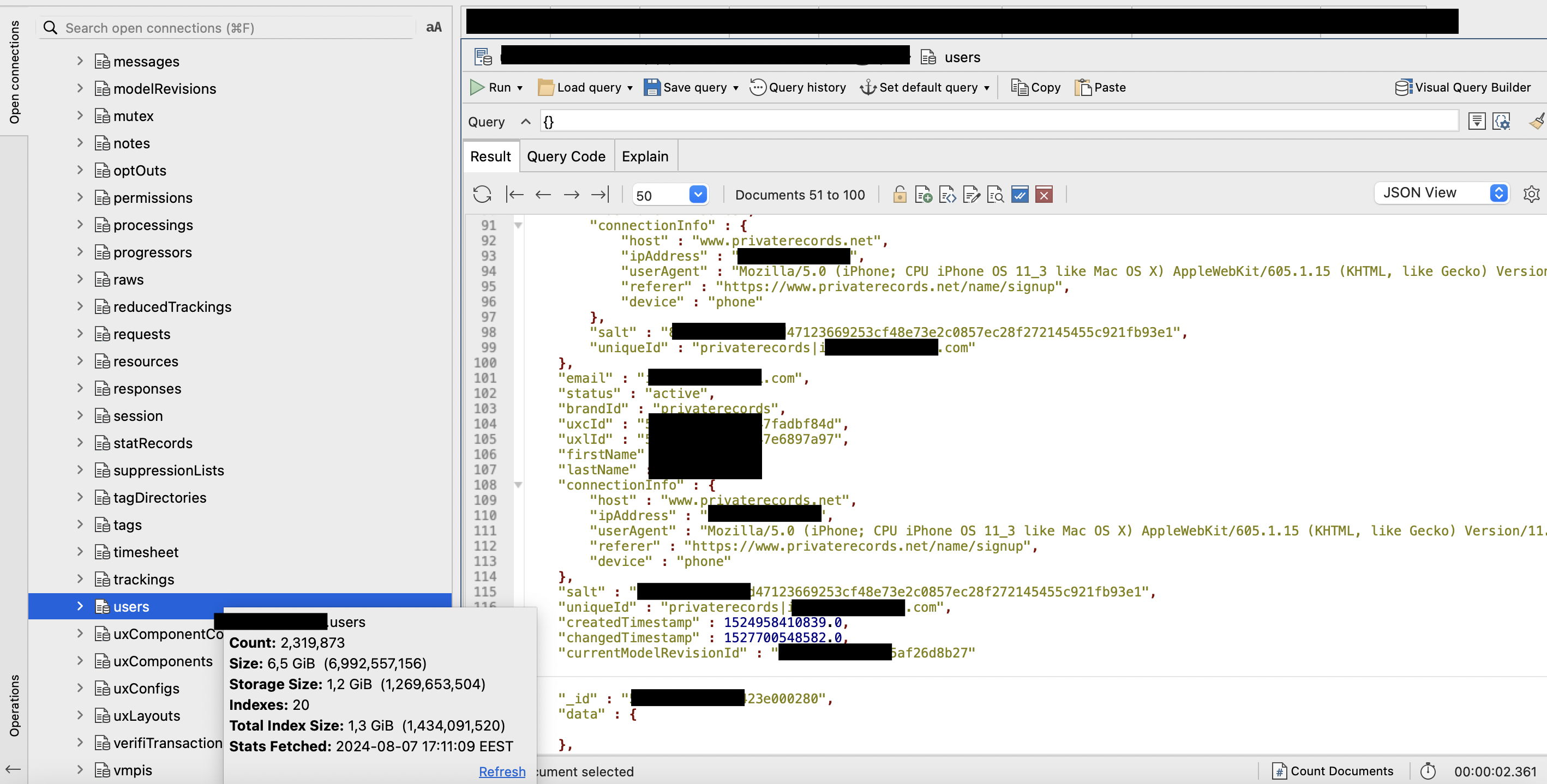
A recent Cybernews study found that a company exposed a database containing 2.2TB of sensitive data, leaving it unprotected and accessible online.
A human error likely exposed over 106 million records with private information about US citizens, affecting at least 100 million individuals and raising serious privacy and safety concerns.
The data of 2,319,873 users from MC2 Data services was leaked, compromising those requiring background checks.
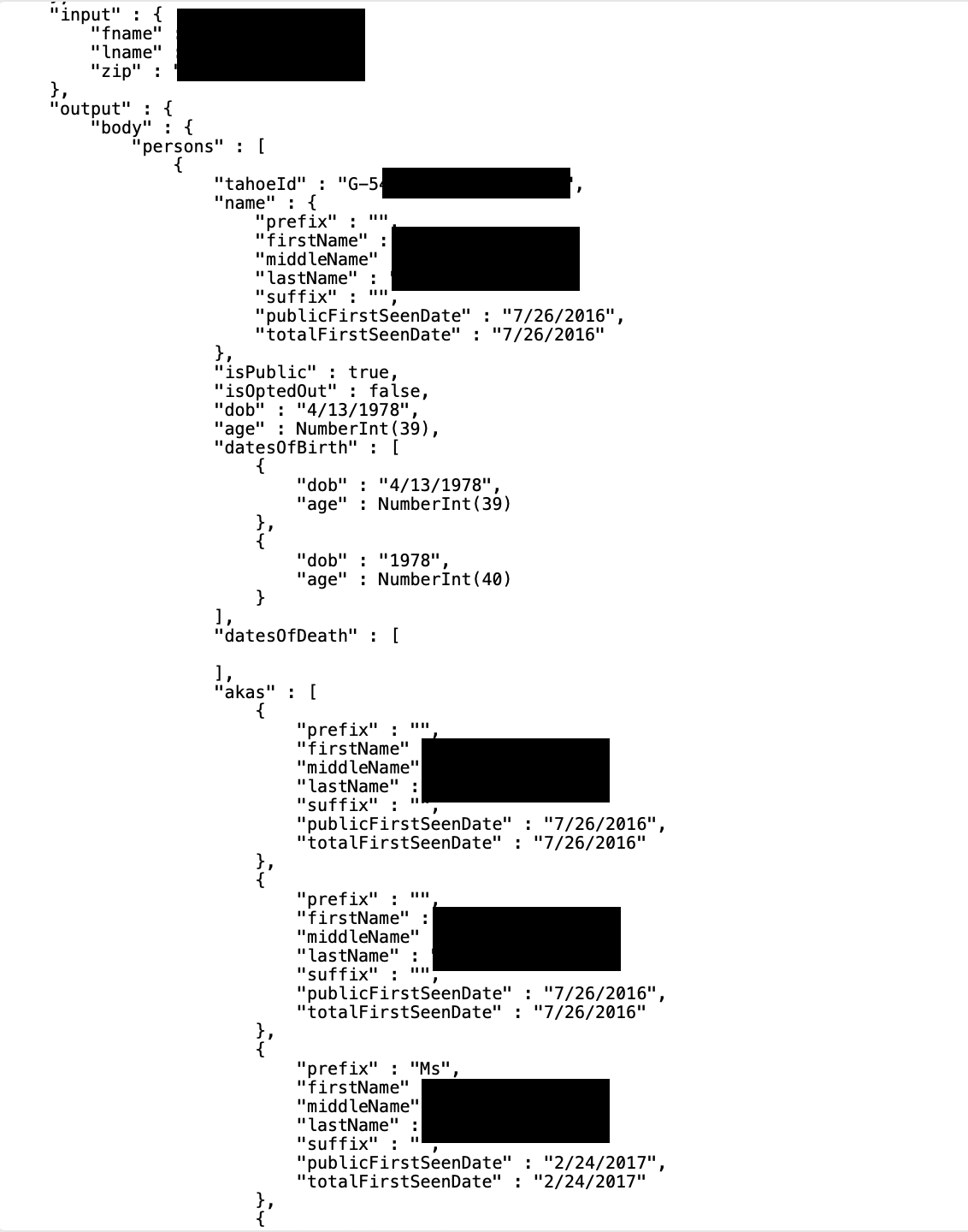
Leaked data included:
Names
Emails
IP addresses
User agents
Encrypted passwords
Partial payment information
Home addresses
Dates of birth
Phone numbers
Property records
Legal records
Property records
Family, relatives, neighbors data
Employment history
Putting countless individuals at risk:
Businesses offering public records and background check services must follow strict regulations at the federal, state, and local levels to ensure legal operations and protect individuals’ data.
The leak found by the Cybernews team raises serious concerns about how organizations handle sensitive data. The exposure of a significant amount of personally identifiable information (PII) compromises privacy and increases the risk of identity theft. Additionally, MC2 Data could face reputational harm and legal consequences.
“Background-checking services have always been problematic, as cybercriminals would often be able to purchase their services to gather data on their victims,” said Aras Nazarovas, a Cybernews security researcher.
“While background-check services keep trying to prevent such cases, they haven’t been able to stop such use of their services completely. Such a leak is a goldmine for cybercriminals as it eases access and reduces risk for them, allowing them to misuse these detailed reports more effectively.”
According to Cybernews researchers, the leaked subscribers’ information is also troublesome, as they could be high-value targets for cybercriminals. These subscribers could be employers, landlords, law enforcement, and similar entities.
“If anyone else accessed this information, it could spark conflicts in some communities and organizations,” adds the researcher. Cybernews contacted MC2 Data for a comment but has not yet received a response.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














