CISA has moved its cyber incident reporting form to the new CISA Services Portal to improve cyber incident reporting. The Portal is a secure platform for reporting cyber incidents. It has extra features like saving and updating reports, sharing with others, and searching and filtering. Users can now have informal …
Read More »How AitM Phishing Attacks Bypass EDR and MFA-How to Fight (Video)
Attackers are using more phishing toolkits (open-source, commercial, and criminal) to carry out adversary-in-the-middle attacks. Attackers can use AitM to steal both login information and active sessions. This lets them bypass security measures like MFA, EDR, and email filtering. What is AitM phishing? AitM phishing uses specialized tools to intercept …
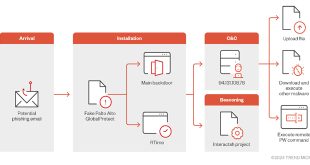
Read More »Hacker to use fake Palo Alto GlobalProtect Tool in cyber attack
Trend Micro researchers identified a sophisticated malware campaign that aims at Middle East organizations. The campaign tricks victims into infecting their devices by pretending to be a real Palo Alto GlobalProtect VPN client. The attack begins with the distribution of a malicious file named “setup.exe,” which masquerades as a legitimate …
Read More »Mirai Botnet Exploits Zero-Day Vulnerability CVE-2024-7029
Akamai’s Security Intelligence Response Team (SIRT) found a large Mirai botnet campaign that is using a new zero-day vulnerability (CVE-2024-7029) in AVTECH IP cameras. The vulnerability, which allows for remote code execution, has been leveraged to propagate a Mirai variant dubbed “Corona,” raising significant concerns about critical infrastructure security. CVE-2024-7029 …
Read More »BlackByte Ransomware Exploits VMware ESXi Flaw
The BlackByte ransomware group is suspected of using a recently fixed security issue in VMware ESXi hypervisors. They are also taking advantage of weak drivers to bypass security measures. A vulnerability named CVE-2024-37085 lets attackers bypass authentication on VMware ESXi systems connected to an Active Directory domain. By using this …
Read More »Google Cloud Leak Exposed Data of 83,000 Shark Tank Contestant
A Google Cloud Storage bucket linked to Alice’s Table, a Shark Tank contestant offering virtual floral arrangement classes, has leaked personal data of over 83,000 customers. Cybernews and Cyble researchers found a misconfigured cloud bucket while investigating. Researchers found that the Google bucket belonged to Alice’s Table, a company founded …
Read More »
CVE-2024-38856
CISA Issues Alert for Actively Exploited Apache OFBiz Vulnerability
CISA issued a warning about a security flaw in Apache OFBiz, an ERP system. The vulnerability is being actively exploited and has been added to CISA’s Known Exploited Vulnerabilities catalog as CVE-2024-38856. CVE-2024-38856 is a serious security flaw in Apache OFBiz. It allows attackers to run code on a remote …
Read More »Chinese Volt Typhoon hackers exploited Versa zero-day breaching ISPs, MSPs
Lumen Technologies’ malware hunters have discovered Chinese APT group Volt Typhoon using a new zero-day exploit in Versa Director servers. They used this exploit to steal credentials and gain unauthorized access to the networks of downstream customers. CVE-2024-39717 is a serious vulnerability that CISA added to their must-patch list after …
Read More »SonicWall Issues Critical Patch for Firewall Vulnerability
SonicWall released security updates to fix a critical flaw in its firewalls. If exploited, this flaw could give unauthorized access to malicious actors. The vulnerability is known as CVE-2024-40766 and has a CVSS score of 9.3. It is an access control issue. “An improper access control vulnerability has been identified …
Read More »NSA Unveils Best Practices for Event Log & Threat Detection – 2024
NSA has released Best Practices for Event Logging and Threat Detection to make sure important systems keep working. These practices apply to cloud services, enterprise networks, mobile devices, and operational technology networks. The Cybersecurity Information Sheet (CSI) was created with international co-authors, including the Australian Signals Directorate’s Australian Cyber Security …
Read More » InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind