Apple has issued urgent security updates to fix a zero-day vulnerability that is being actively exploited, warning that attackers may have used it in targeted campaigns.
CVE-2025-43300 is a flaw in Apple’s Image I/O framework that allows out-of-bounds writing, affecting how applications manage common image file formats.
By infosecbulletin
/ Sunday , September 21 2025
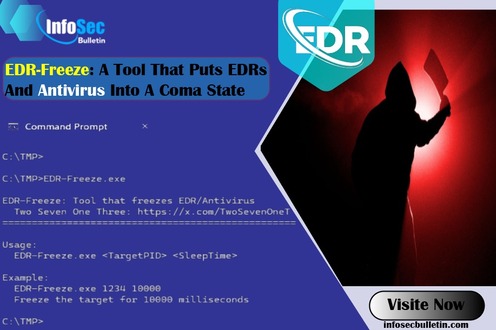
A new proof-of-concept tool named EDR-Freeze has been developed, capable of placing Endpoint Detection and Response (EDR) and antivirus solutions...
Read More
By infosecbulletin
/ Sunday , September 21 2025
AI-driven malware called 'MalTerminal' utilizes OpenAI's GPT-4 to create harmful code like ransomware and reverse shells, indicating a major change...
Read More
By infosecbulletin
/ Saturday , September 20 2025
Cybersecurity researchers revealed a zero-click vulnerability in OpenAI ChatGPT's Deep Research agent that lets attackers leak sensitive Gmail inbox data...
Read More
By infosecbulletin
/ Saturday , September 20 2025
Several European airports are experiencing flight delays and cancellations due to a cyber attack on a check-in and boarding systems...
Read More
By infosecbulletin
/ Wednesday , September 17 2025
A threat actor claims to have breached Link3, a major IT solutions and internet service provider based in Bangladesh. The...
Read More
By infosecbulletin
/ Wednesday , September 17 2025
Check point, a cyber security solutions provider hosts an event titled "securing the hyperconnected world in the AI era" at...
Read More
By infosecbulletin
/ Tuesday , September 16 2025
Cross-Site Scripting (XSS) is one of the oldest and most persistent vulnerabilities in modern applications. Despite being recognized for over...
Read More
By infosecbulletin
/ Monday , September 15 2025
Every day a lot of cyberattack happen around the world including ransomware, Malware attack, data breaches, website defacement and so...
Read More
By infosecbulletin
/ Monday , September 15 2025
A critical permission misconfiguration in the IBM QRadar Security Information and Event Management (SIEM) platform could allow local privileged users...
Read More
By infosecbulletin
/ Monday , September 15 2025
Australian banks are now using bots to combat scammers. These bots mimic potential victims to gather real-time information and drain...
Read More
According to Apple’s advisory:
“Apple is aware of a report that this issue may have been exploited in an extremely sophisticated attack against specific targeted individuals.”
The vulnerability lets attackers create harmful image files that, when used by a vulnerable application, could cause memory corruption. This could allow them to execute arbitrary code, leading to surveillance or device compromise.
Apple explained the fix as follows:
“An out-of-bounds write issue was addressed with improved bounds checking. Processing a malicious image file may result in memory corruption.”
The company has released patches across its ecosystem, urging all users to apply them immediately:
iOS 18.6.2 and iPadOS 18.6.2
iPadOS 17.7.10
macOS Sequoia 15.6.1
macOS Sonoma 14.7.8
macOS Ventura 13.7.8
This wide coverage underscores how deeply integrated the Image I/O framework is across Apple products.
As is common with zero-day disclosures, Apple has not shared technical details about the exploitation, the identity of the attackers, or the profile of the victims. The zero-day is being leveraged in precision-targeted campaigns, potentially linked to spyware operations or nation-state threat actors.
With CVE-2025-43300 marked as actively exploited, users are strongly advised to:
Update immediately to the latest iOS, iPadOS, and macOS versions.
Be cautious when receiving unexpected images or opening files from untrusted sources.
Copilot Breaks Your Audit Log, but Microsoft Won’t Tell the customer
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind