Apple warned users in 91 other countries about a possible “mercenary spyware attack”. Apple notified Reuters that the company found evidence of attackers attempting to remotely compromise iPhones.
Mercenary spyware attacks are rare but much more sophisticated than regular cybercriminal activity or malware, as stated in the email.
Apple also specifically called out companies like NSO Group for developing commercial surveillance tools such as Pegasus that are used by state actors to pull off “individually targeted attacks of such exceptional cost and complexity.”
“Though deployed against a very small number of individuals — often journalists, activists, politicians, and diplomats — mercenary spyware attacks are ongoing and global,” Apple said.
“The extreme cost, sophistication, and worldwide nature of mercenary spyware attacks makes them some of the most advanced digital threats in existence today.”
TechCrunch reported that Apple sent threat notifications to iPhone users in 92 countries at 12:00 p.m. PST on Wednesday, alongside a revision to the support page.
Last month, the U.S. government announced that Finland, Germany, Ireland, Japan, Poland, and South Korea have joined a group of 11 countries working to develop protections against the misuse of invasive surveillance technology.
“Commercial spyware has been misused across the world by authoritarian regimes and in democracies […] without proper legal authorization, safeguards, or oversight,” the governments said in a joint statement.
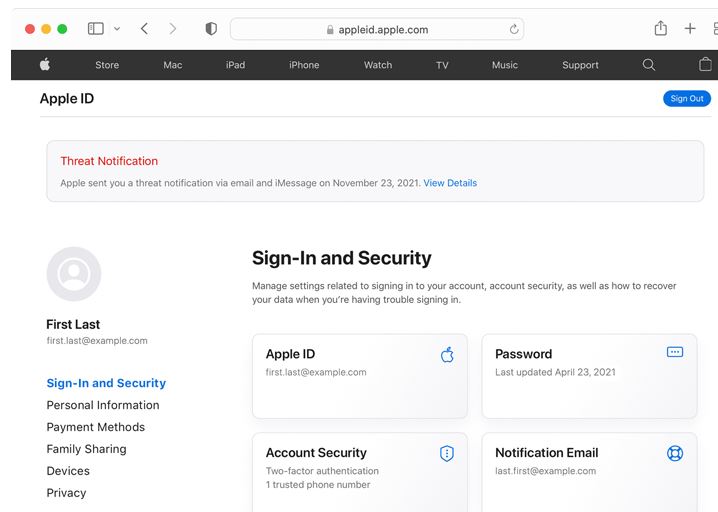
Apple said, It threat notifications will never ask you to click any links, open files, install apps or profiles, or provide your Apple ID password or verification code by email or on the phone. To verify that an Apple threat notification is genuine, sign in to appleid.apple.com. If Apple sent you a threat notification, it will be clearly visible at the top of the page after you sign in.
All users should continue to protect themselves from cybercriminals and consumer malware by following best practices for security:
Update devices to the latest software, as that includes the latest security fixes
Protect devices with a passcode
Use two-factor authentication and a strong password for Apple ID
Install apps from the App Store
Use strong and unique passwords online
Don’t click on links or attachments from unknown senders
If you have not received an Apple threat notification, but have good reason to believe you may be targeted, you can enable Lockdown Mode on your Apple devices to help protect against highly sophisticated attacks. If you require emergency cybersecurity assistance for other reasons, we strongly suggest you enlist expert help. The Consumer Reports Security Planner website offers a list of emergency resources that may be able to assist you.
Apple has sent threat notifications multiple times a year since 2021. The company has informed users in more than 150 countries about this.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














