In January 2025, there were 510 global ransomware incidents, with Akira as the leading group and new ones like MORPHEUS and Gd Lockersec appearing. The Manufacturing sector was the main target, followed by Finance and IT, with the USA being the most affected region. This report highlights key ransomware trends, showing that threat actors are becoming more sophisticated and spreading their focus internationally, underscoring the need for improved cybersecurity measures.
In January 2025, ransomware attacks decreased slightly, but their frequency and complexity stayed the same. This report analyzes ransomware trends from recent months, identifying the most impacted industries and regions, as well as new ransomware groups. It also explores the evolving tactics of major threat actors, including Python malware and VMware ESXi exploitation, providing insights into the changing cyber threat landscape.
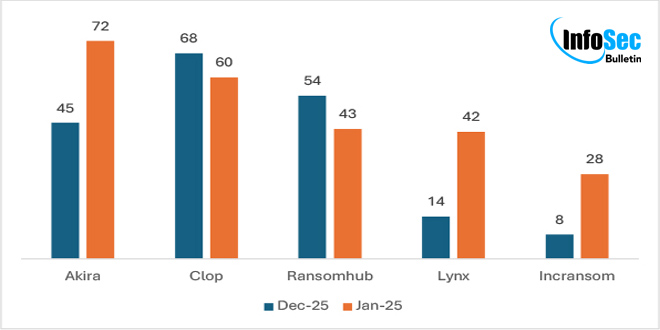
TREND COMPARISON OF JANUARY 2025’s TOP 5 RANSOMWARE GROUPS:
In January 2025, several ransomware groups were very active. Here are the trends for the top 5:
In January 2025, Akira’s activity increased by 60%, while Lynx and Incransom rose by 200% and 250%, respectively. Conversely, Cl0p declined by 12% and RansomHub fell by 20%. These trends indicate changes in the ransomware landscape and the priorities of threat actors across industries.
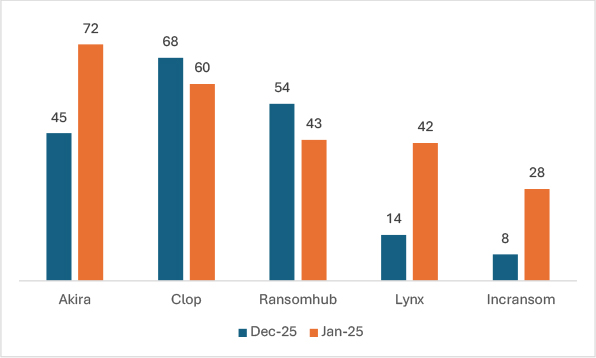
INDUSTRIES TARGETED IN JANUARY 2025 COMPARED WITH DECEMBER 2024:
The graph shows ransomware trends in January 2025 compared to December 2024. Ransomware attacks on IT increased by 60% due to sensitive data access, while healthcare saw a 31.25% rise for similar reasons. Education and Transportation experienced significant increases of 93% and 69%, respectively, due to their growing digital presence. FMCG and Hospitality had slight increases of 8% and 5%. In contrast, Banking & Finance dropped by 54%, and Manufacturing declined by 2.6%. These trends emphasize the need for strong cybersecurity measures across all industries.
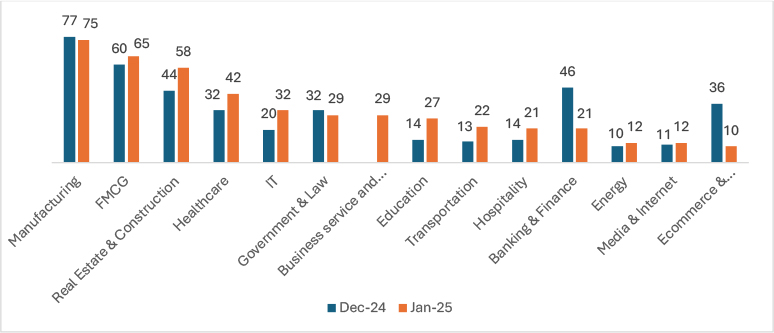
TREND COMPARISON OF RANSOMWARE ATTACKS
In January 2025, there was a 3.95% drop in victims compared to December 2024. However, the long-term trend is concerning, with victims increasing from 205 in 2023 to 280 in 2024, and jumping to 510 in 2025—an 82.14% rise. This surge emphasizes the increasing threat of ransomware, driven by changing tactics and a focus on critical industries.
GEOGRAPHICAL TARGETS: TOP 5 LOCATIONS
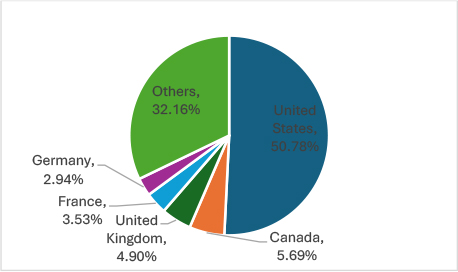
In January 2025, ransomware attacks were predominantly in the United States (259), followed by Canada (29), the United Kingdom (25), France (18), and Germany (15). These areas are targeted because of their strong economies, data-rich businesses, critical infrastructure, and high likelihood of paying ransoms.
EMERGING GROUPS:
MORPHEUS:
Researchers have discovered a new ransomware called Morpheus, which may have been active since late December 2024, but has only publicly listed victims on a data leak site since January 2025. As of this report, the group has claimed three victims.
Gd Lockersec:
By January 2025, researchers noted the launch of a leak site by Gd Lockersec, a new ransomware group focused on financial gain. They prohibit attacks on entities from CIS countries, Cuba, North Korea, and China, as well as non-profit hospitals and certain organizations. Companies that have already paid a ransom are also exempt from further attacks.
During the drafting of this report, the group has claimed 5 victims.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind