Fortinet has released patches to address a critical vulnerability in its FortiNAC network access control solution. The vulnerability, tracked as CVE-2023-33299, is a deserialization of untrusted data issue that could allow an unauthenticated attacker to execute unauthorized code or commands on affected devices.
The vulnerability impacts FortiNAC versions up to 7.2.1, up to 9.4.2, up to 9.2.7, and up to 9.1.9, as well as all 8.x iterations. Fortinet has addressed the vulnerability with the release of FortiNAC versions 9.4.3, 9.2.8, 9.1.10, and 7.2.2.
By infosecbulletin
/ Friday , May 9 2025
Microsoft has fixed critical vulnerabilities in its core cloud services, including Azure Automation, Azure Storage, Azure DevOps, and Microsoft Power...
Read More
By infosecbulletin
/ Thursday , May 8 2025
The cyber threat landscape is rapidly changing, with a notable increase in ransomware activity in April 2025, driven by the...
Read More
By infosecbulletin
/ Thursday , May 8 2025
SonicWall has released patches for three security flaws in SMA 100 Secure Mobile Access appliances that could allow remote code...
Read More
By infosecbulletin
/ Thursday , May 8 2025
From April 2024 to April 2025, Flashpoint analysts noted that the financial sector was a major target for threat actors,...
Read More
By infosecbulletin
/ Thursday , May 8 2025
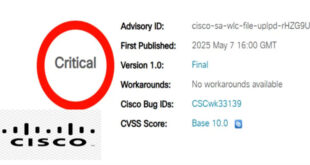
Cisco has issued a security advisory for a critical vulnerability in its IOS XE Software for Wireless LAN Controllers (WLCs)....
Read More
By infosecbulletin
/ Wednesday , May 7 2025
Attackers linked to the Play ransomware operation deployed a zero-day privilege escalation exploit during an attempted attack against an organization...
Read More
By infosecbulletin
/ Wednesday , May 7 2025
Hackers are exploiting an unauthenticated remote code execution vulnerability in the Samsung MagicINFO 9 Server to take control of devices...
Read More
By infosecbulletin
/ Tuesday , May 6 2025
CISA added the Langflow vulnerability, CVE-2025-3248 (CVSS score 9.8), to its Known Exploited Vulnerabilities catalog. Langflow is a popular tool...
Read More
By infosecbulletin
/ Tuesday , May 6 2025
Google has released its monthly Android security updates, addressing 46 vulnerabilities, including one that has been actively exploited. CVE-2025-27363 (CVSS...
Read More
By infosecbulletin
/ Tuesday , May 6 2025
The Cyber Security Club, representing the Department of Computer Science and Engineering at the University of Asia Pacific (UAP), has...
Read More
ALSO READ:
Google chrome patched 4 high vulnerabilities
The vulnerability was discovered by security researcher Florian Hauser of Code White. Hauser notes that there are few organizations exposing TCP port 1050 to the public internet, and that one of the organizations he identified removed the vulnerable services a few days after he reported them to CISA.
In addition to the RCE vulnerability, Hauser also identified and reported CVE-2023-33300, a medium-severity command injection vulnerability. This vulnerability can be exploited by an unauthenticated attacker to copy local files from the device to other local directories. However, access to the copied data is only possible if the attacker has an existing foothold and enough privileges on the device.
This vulnerability was also resolved with the release of FortiNAC versions 9.4.4 and 7.2.2.
Fortinet has not yet seen any evidence of these vulnerabilities being exploited in attacks. However, it is not uncommon for threat actors to target security defects in Fortinet products for which patches have been released.
Organizations that are using affected versions of FortiNAC should update to the latest versions as soon as possible to mitigate the risk of exploitation.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind