GreyNoise has detected a sharp increase in login scanning aimed at Palo Alto Networks PAN-OS GlobalProtect portals. In the past 30 days, nearly 24,000 unique IP addresses have tried to access these portals. This indicates a coordinated attempt to test network defenses and find vulnerable systems, possibly as a step before targeted attacks.
Recent observations by GreyNoise indicate that this activity may point to new vulnerabilities emerging soon:
“Over the past 18 to 24 months, we’ve observed a consistent pattern of deliberate targeting of older vulnerabilities or well-worn attack and reconnaissance attempts against specific technologies,” said Bob Rudis, VP of Data Science at GreyNoise. “These patterns often coincide with new vulnerabilities emerging 2 to 4 weeks later.”
Key Observations:
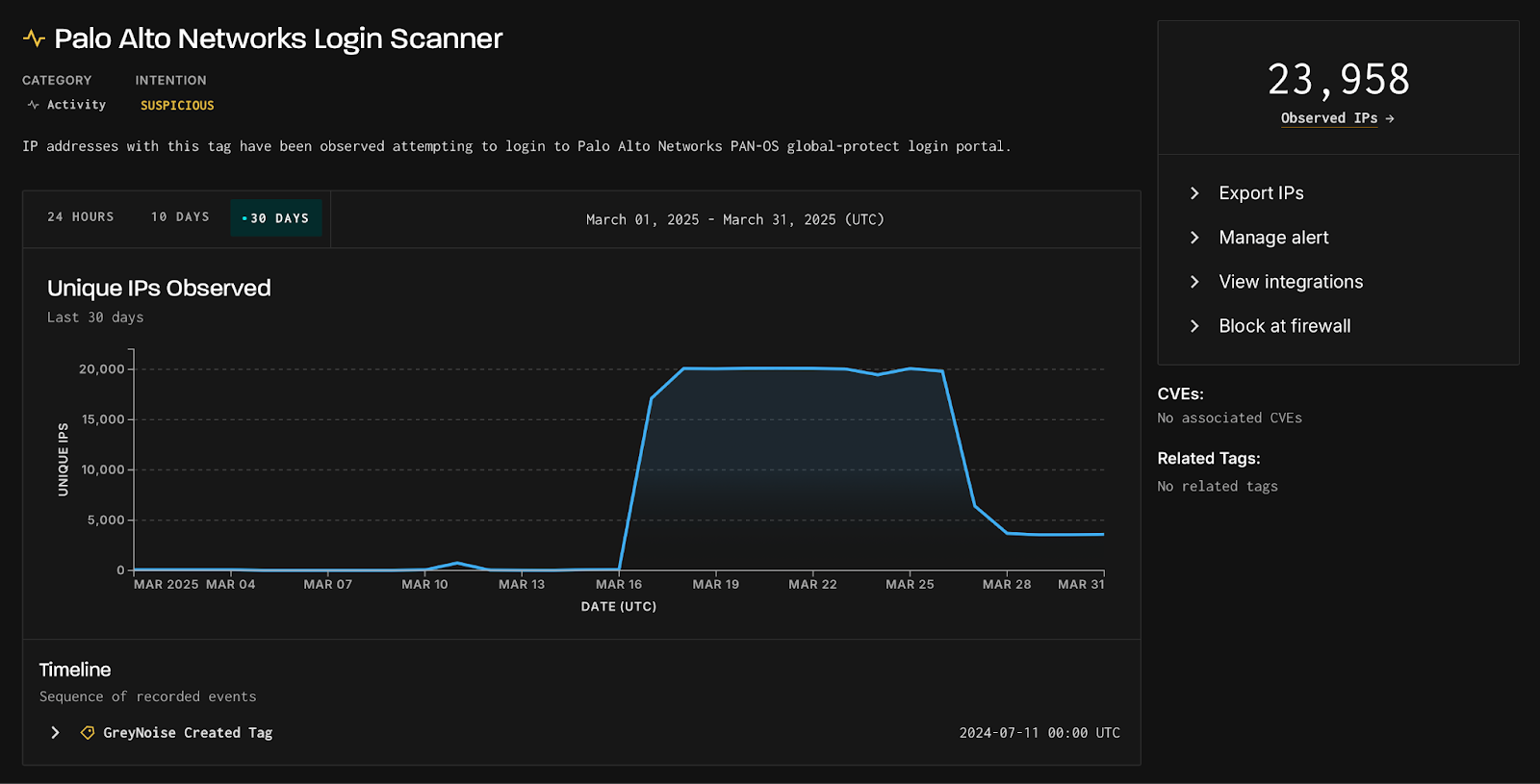
The spike began on March 17, 2025, with activity peaking at nearly 20,000 unique IPs per day and remaining steady until March 26 before tapering off.
Most of the observed activity is classified as suspicious (23,800 IPs), with a smaller subset flagged as malicious (154 IPs).
The consistency of this activity suggests a planned approach to testing network defenses, potentially paving the way for exploitation. Organizations using Palo Alto Networks products should take steps to secure their login portals.
Researchers claimed that a large portion of traffic is linked to 3xK Tech GmbH (20,010 IPs) under ASN200373. Other key contributors are PureVoltage Hosting Inc., Fast Servers Pty Ltd., and Oy Crea Nova Hosting Solution Ltd.
Additionally, GreyNoise has identified three JA4h hashes linked to the login scanner tool:
po11nn11enus_967778c7bec7_000000000000_000000000000
po11nn09enus_fb8b2e7e6287_000000000000_000000000000
po11nn060000_c4f66731b00d_000000000000_000000000000
These hashes show common connection patterns used by the login scanner tool, helping GreyNoise track and link different login attempts from the same toolkit.
Source and Destination Analysis:
Source Countries: Predominantly originating from the United States (16,249) and Canada (5,823), followed by Finland, Netherlands, and Russia.
Destination Countries: The overwhelming majority of traffic targeted systems in the United States (23,768), with smaller volumes directed toward the United Kingdom, Ireland, Russia, and Singapore.
These patterns reflect the global nature of the activity, indicating that multiple regions are being targeted.
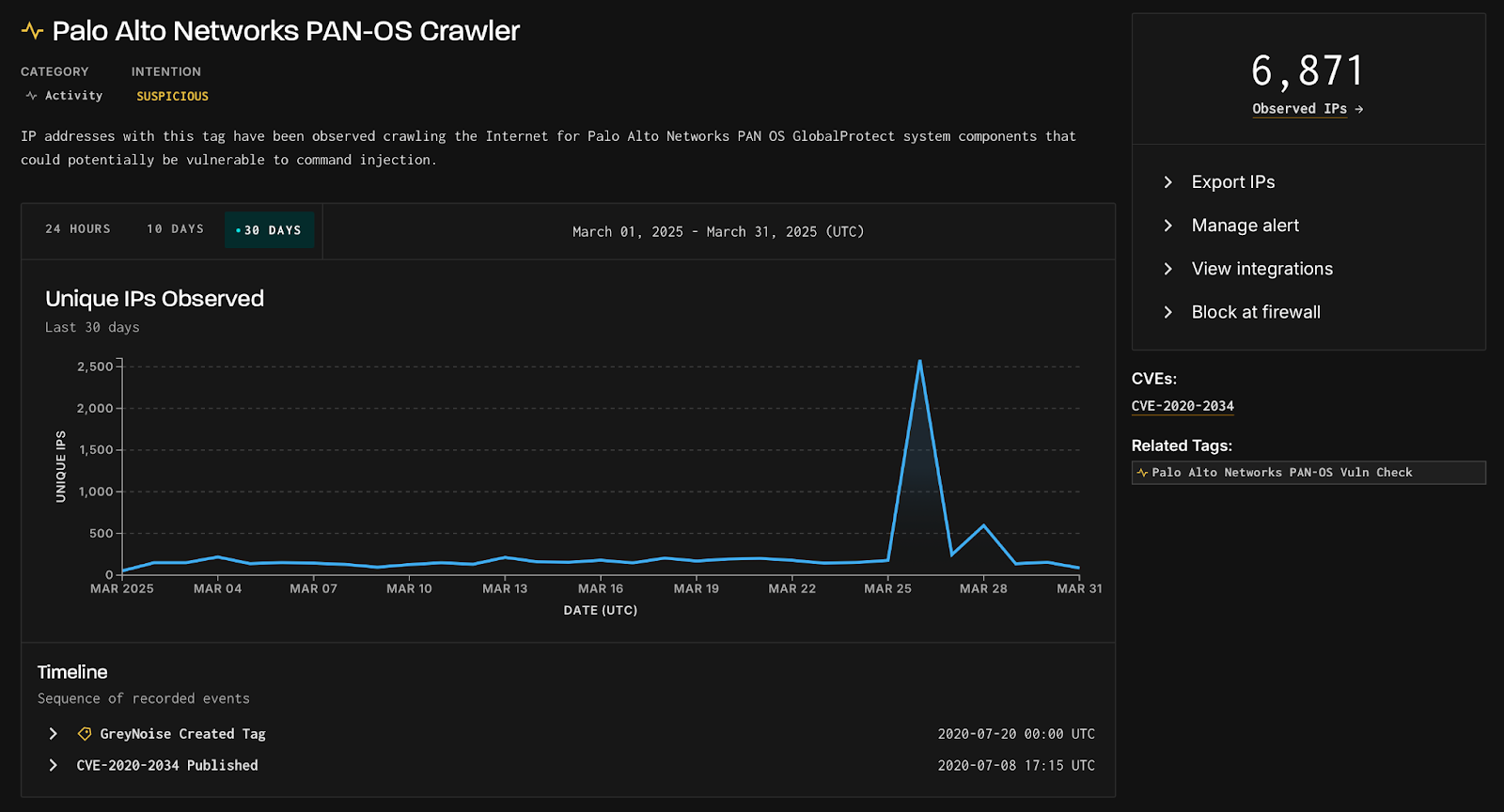
Concurrent Crawler Activity Detected:
The activity is associated with other PAN-OS reconnaissance tags, like PAN-OS Crawler, which saw a spike of 2,580 unique source IPs on March 26, 2025.
Reminiscent of 2024 Espionage Campaign:
The recent activity mirrors a 2024 espionage campaign on perimeter network devices, as reported by Cisco Talos. Although the methods vary, both cases emphasize the need to monitor and secure critical edge devices from unauthorized access.
Organizations using Palo Alto Networks products should review their March logs, enhance monitoring, conduct threat hunting, apply all security patches, and consider blocking any identified malicious IPs.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind