15,000 Go module repositories on GitHub are vulnerable to repojacking attack, according to new research. VulnCheck chief technology officer jacob Baines shared a report with renowned newspaper where he said, “More than 9,000 repositories are vulnerable to repojacking due to GitHub username changes, “More than 6,000 repositories were vulnerable to repojacking due to account deletion.”
Repojacking is a type of attack where a malicious actor takes advantage of changes or deletions to an account username to create a repository with the same name and username. This is done to carry out open-source software supply chain attacks.
ALSO READ:
Microsoft warns of exploiting critical outlook vulnerability
Cloud security company Aqua recently warned that many software repositories on GitHub could be at risk due to a specific threat. They advised organizations that change their names to protect themselves by making sure they still own their previous name as placeholders.
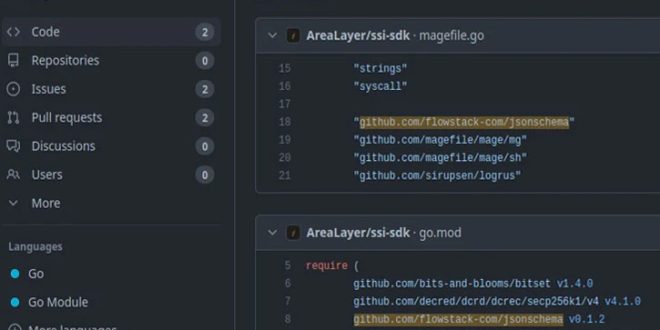
Go modules are vulnerable to repojacking because they are decentralized and published to version control platforms like GitHub or Bitbucket, unlike npm or PyPI.
“Anyone can then instruct the Go module mirror and pkg.go.dev to cache the module’s details,” Baines said. “An attacker can register the newly unused username, duplicate the module repository, and publish a new module to proxy.golang.org and go.pkg.dev.”
GitHub has a way to stop developers from using packages that could be unsafe. It’s called popular repository namespace retirement. This prevents people from creating repositories with names that are no longer used and have been cloned over 100 times before the owners’ accounts were renamed or deleted.
According to VulnCheck, this protection is not useful for Go modules because they are cached by the module mirror. This means that there is no need to interact with or clone a repository. Therefore, popular Go-based modules could have been cloned less than 100 times, allowing for a bypass.
“Unfortunately, mitigating all of these repojackings is something that either Go or GitHub will have to take on,” Baines said. “A third-party can’t reasonably register 15,000 GitHub accounts. Until then, it’s important for Go developers to be aware of the modules they use, and the state of the repository that the modules originated from.”
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind